3 Steps for Continuous Improvement in Cloud Security
Blog Article Published: 12/06/2021
 This blog was originally published by JupiterOne here.
This blog was originally published by JupiterOne here.
Written by Ashleigh Lee, JupiterOne.
Relationships make life rich. Together, we can do so much more than a single person alone – inspire change on micro and macro levels, recover and restore hope from storms, practice empathy and compassion for the things we don’t understand, and innovate in ground-breaking, disruptive ways.
In life, it is often the relationships we have with others that drive us to continuously improve. Relationships bring about a better self-awareness, if we allow them to shine a light in our lives.
There are so many relationships in cloud environments – users have access to infrastructure systems that run production code that is built with open source code that has an issue with exposing customer data in cleartext which creates risk for the business and puts them out of compliance for HIPAA, FFIEC, GDPR, PCI, etc. It’s all one big interconnected network of relationships!
So where do we start to continuously improve the security of our cloud environments?
1. Discover more ALL of your cloud environment
The first step to continuously improve cloud security is to discover ALL of the cyber assets that currently exist in your environment. Sure, you could go from system to system and pull a list of every database, identity, code repo, etc. But wouldn’t it be easier to just have a place that pulls in that information automatically and continuously?
Invest a lot of resources into building integrations that can ingest and normalize cyber asset data for you. Every point solution has its own structure and way of storing data, and it is incredibly time intensive to standardize data across multiple systems.
“I love drowning in lists and Excel spreadsheets,” said no system admin ever.
2. Understand the relationships across cyber assets
Sometimes we’re focused so heavily on executing and performing that we don’t tend to the relationships, the interconnectedness, that make the business run. These are the relationships that attackers take advantage of when they’re trying to reach the gold mine at the core of your business – personal data and intellectual property.
Understanding these relationships, growing in self-awareness, and seeing the gaps can be overwhelming, but knowledge is power. As we discover more, see more, know more, we develop ways to respond and have less to fear.
As we normalize the data from your various systems, we use relationship language like CONTAINS, USES, MANAGES, OWNS, EVALUATES and more. Check out more of the relationship verbs here.
3. Monitor and act to achieve continuous security and policy as code
From a 30,000 foot view down to the metadata of each cyber asset, explore the relationships between accounts, permissions, areas of exposure, and owners of the systems. Teams can monitor activity in a single system of record with contextual data to fix any out-of-band activities that force your environments out of compliance
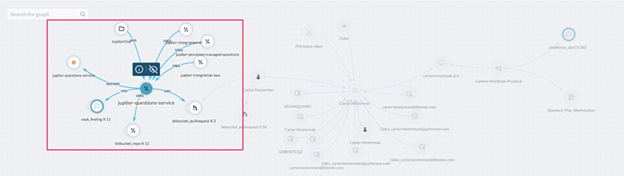
Source: Cyber Asset Relationships Matter – Part Two – Analyzing Relationship Mapping
By gaining visibility into all of your cyber asset relationships in one platform, security and infrastructure teams can visually explore and analyze the business impact of exposure, prioritize remediation, as well as trace the steps of an attacker when incidents occur. Teams can more effectively enforce policies and procedures, quickly gather evidence of compliance, and monitor for continuous governance and security.
Teams must build a holistic security program looking across all cyber assets and their relationships while committing to continuous improvement.
You are not alone in the journey to securing your cloud environments. All of us – your team, JupiterOne, other security and IT professionals – are unified in purpose, but autonomous in execution. Be better than the attackers who try to breach your environment. Know more, fear less.
Trending This Week
#1 The 5 SOC 2 Trust Services Criteria Explained
#2 What You Need to Know About the Daixin Team Ransomware Group
#3 Mitigating Security Risks in Retrieval Augmented Generation (RAG) LLM Applications
#4 Cybersecurity 101: 10 Types of Cyber Attacks to Know
#5 Detecting and Mitigating NTLM Relay Attacks Targeting Microsoft Domain Controllers
Related Articles:
How to Prepare Your Workforce to Secure Your Cloud Infrastructure with Zero Trust
Published: 04/24/2024
Neutralizing the Threat with Cloud Remediation
Published: 04/23/2024
10 Tips to Guide Your Cloud Email Security Strategy
Published: 04/17/2024
The Widening Overlap Between Cloud Workloads and Cybersecurity
Published: 04/17/2024






