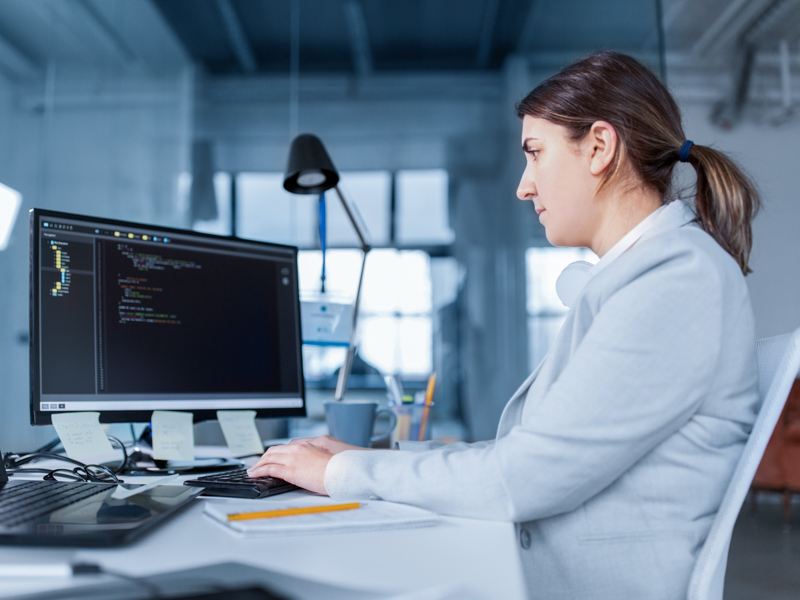
Blog
Read the latest cloud security news, trends, and thought leadership from subject matter experts.

Core Cloud
‘Leaky Vessels’ Docker Vulnerabilities Found in Many Cloud Environments: RunC (60%) and BuildKit (28%)
Published: 04/23/2024

Core Cloud
Detecting and Mitigating CVE-2023-4911: Local Privilege Escalation Vulnerability
Published: 02/01/2024

Future Cloud
Predicting Monthly CVE Disclosure Trends for 2024: A Time Series (SARIMAX) Approach
Published: 01/19/2024

Core Cloud
How Malicious Insiders Use Known Vulnerabilities Against Their Organizations
Published: 01/11/2024
.jpg)
Core Cloud
MOVEit Exploit & Ransomware Attack: Why SaaS Security Is Critical During a Cyberattack
Published: 11/08/2023

Core Cloud
Discovering and Blocking a Zero-Day Exploit: The Case of CVE-2023-36874
Published: 10/31/2023
.jpg)
Core Cloud
New Container Exploit: Rooting Non-Root Containers with CVE-2023-2640 and CVE-2023-32629, aka GameOver(lay)
Published: 10/17/2023

SCATTERED SPIDER Exploits Windows Security Deficiencies with Bring-Your-Own-Vulnerable-Driver Tactic in Attempt to Bypass Endpoint Security
Published: 03/16/2023

OWASSRF: New Exploit Method Identified for Exchange Bypassing ProxyNotShell Mitigations
Published: 03/01/2023
Filter by Theme
Core Cloud

Core Cloud
Whether you have an established cloud security program or are starting your cloud migration, these blogs will help you enhance your cloud security strategy . Learn about cybersecurity threats, certification, and more.
Cloud Assurance
Cloud Assurance
Improve the security and compliance posture of your organization and leverage the controls inside of cloud assurance. Gain the guidance and tools to build your own cloud assurance ecosystem.
Future Cloud
Future Cloud
Leverage CSA to help your organization solve tomorrow's problems today. Explore innovative technologies and strategies through the topics of Zero Trust, Quantum, and more.



.jpg)