Connected Third-Party Applications Widen Attack Surface Area
Published 10/02/2023
Originally published by Abnormal Security.
Written by Jade Hill.
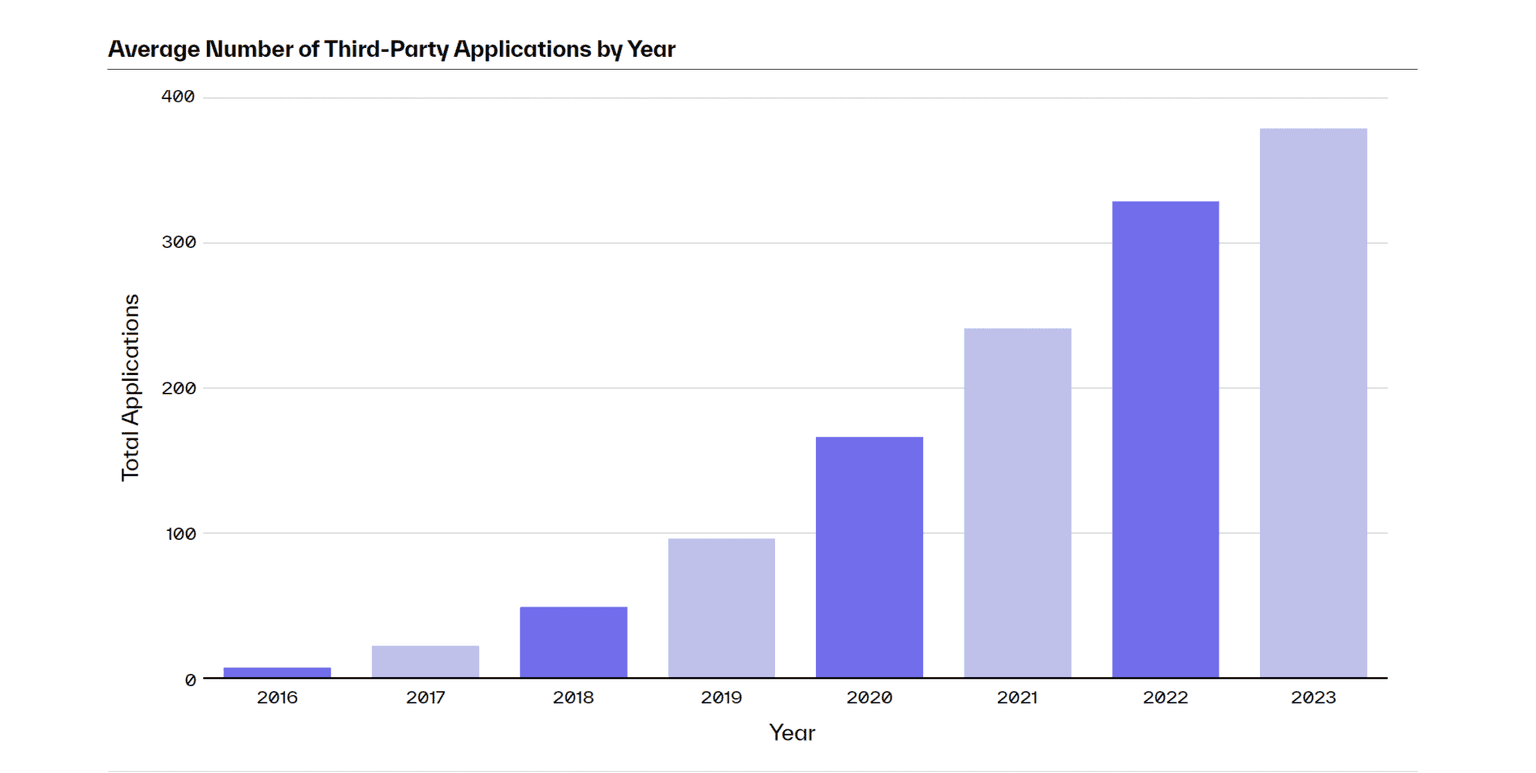
Inbound email attacks are a mainstay for cybercrooks, but criminals are shifting tactics to exploit third-party applications as a new method for gaining entry into an organization’s email environment. This is getting easier due to the popularity of software as a service (SaaS) and apps. In fact, we’ve seen a 128% increase since 2020 in the number of unique applications leveraged by the Abnormal customer base, now totaling more than 26,000 unique apps.
Connected third-party applications aren’t problems in themselves. These tools offer collaboration and efficiency essential for today’s dispersed workforce. But more integrations mean more opportunities for infiltration.
And according to the latest research from IBM, vulnerabilities in third-party software accounted for 13% of all breaches in 2022—costing organizations an average of $4.55 million per incident. Organizations need to understand these vast threat environments to more aptly defend against attacks.
Third-Party Apps Expand the Surface Area for Cyberattacks
Traditional cybersecurity operates like a drawbridge, letting through legitimate emails and preventing malicious emails from entering the organization. Phishing, malware, and social engineering scams would still get through without proper security protocols, but they all entered through the inbox—the front door. Unfortunately, third-party applications provide side doors for attackers to compromise email accounts without detection.
There are a few ways attackers can use third-party apps to breach your organization, but some of the most prevalent include:
- Stealing API keys and installing malicious applications with high-risk permissions
- Tricking employees via social engineering into installing legitimate apps that secretly provide attackers with access
- Stealing customer data from infiltrated and compromised applications
And unfortunately, this isn’t just theoretical. Media giant News Corp—owner of The Wall Street Journal and the New York Post—suffered an undetected cyberattack for two years. During that time, attackers stole a plethora of email data from journalists. How did this happen? A malicious application integrated with their Microsoft 365 cloud email provided attackers with a side door to access sensitive information without detection. And the number of side doors continues to grow.
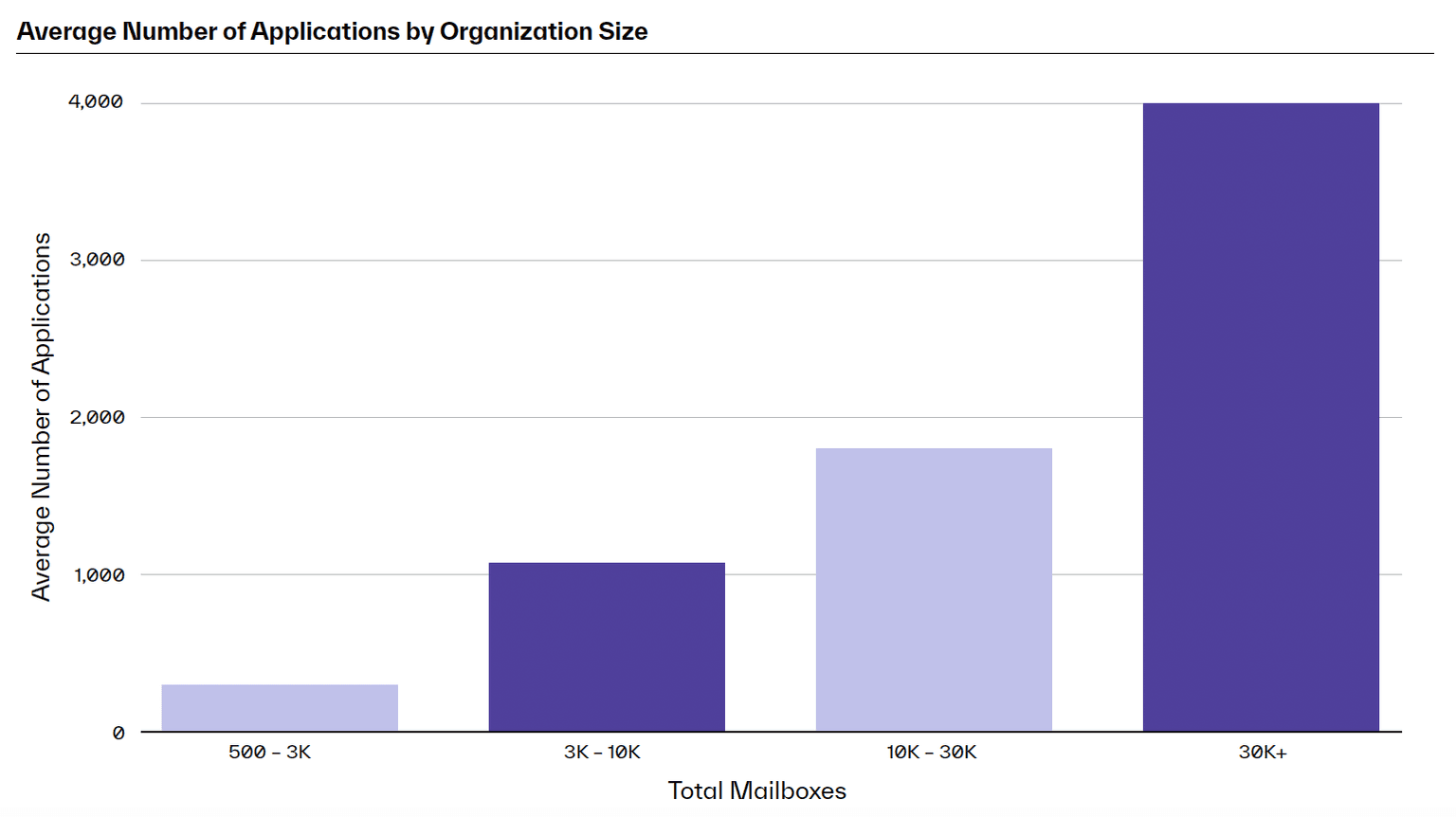
While News Corp might have been specifically targeted, every organization houses valuable information coveted by cybercriminals. The larger the organization, the larger its app portfolio, and thus the larger the surface area for exploitation.
For example, organizations with fewer than 3,000 mailboxes average only a few hundred integrated applications to assist their employees. But organizations hosting more than 30,000 mailboxes use an average of 4,000 applications—demonstrating the herculean task for security teams to protect against incursion.
These attacks are devastating and difficult to detect because they bypass traditional inbound email security tools. The threat surface presented by these apps is ever-expanding, but that doesn’t mean the problem is unstoppable. Securing organizations requires first understanding what applications are connected to email—and what each application has permission to do.
Understanding Third-Party App Permissions and Associated Risks
Every time an employee authorizes a third-party application, they grant it a number of permissions. Many of these operations are legitimate, but when apps are compromised, they give attackers access to things they shouldn’t have. Security teams must recognize the risk level associated with each of these permissions.
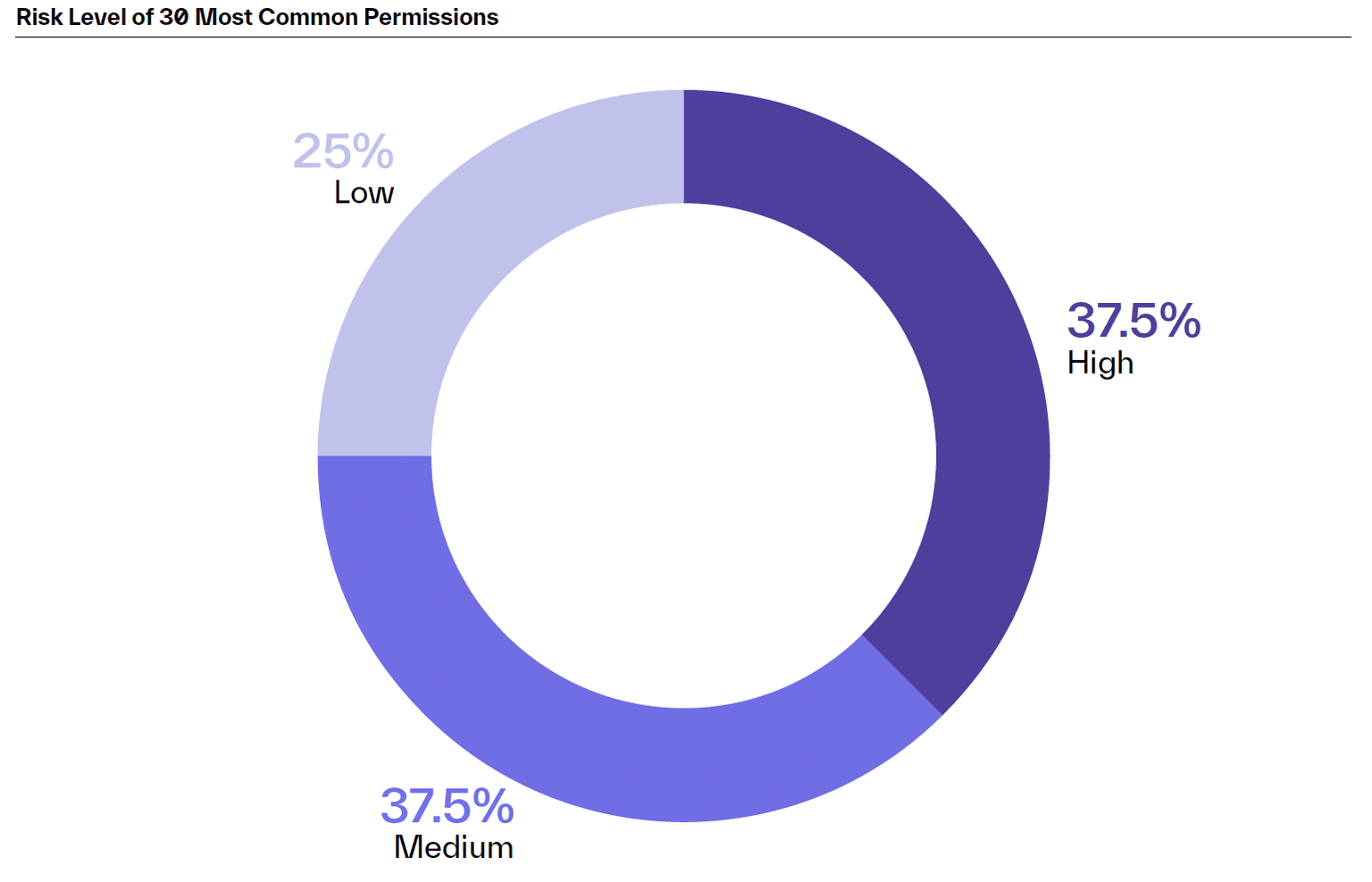
Each third-party application is a potential entry point into your mailboxes. So it’s vital to understand which permissions are most risky. For example:
- Permissions to view calendars are fairly innocuous
- Permissions giving read access to email content is a medium risk since mailboxes, often hold sensitive business information
- Permissions to create or delete content, change permissions, or privilege escalations present high risks
But surely applications don’t actually need all those high-risk permissions, right? Of the top 30 permissions seen by Abnormal, more than 37% are considered high-risk, while another 37% are considered medium-risk.
Recognizing that each application provides attackers with a side door into your email environment is the first important step to securing your organization. Piqued your curiosity? You can see the full list of common applications and their associated risk levels in the report.
Whether bad actors attack through the front door with an inbound email or a side door via a connected third-party application, organizations must defend themselves. Legacy email security tools simply cannot stand up to the challenge.
Unlock Cloud Security Insights
Subscribe to our newsletter for the latest expert trends and updates
Related Articles:
MITRE ATT&CK for Cloud: A Practitioner's Guide to Detection Coverage
Published: 05/22/2026
Patching Faster is Not the Answer to Mythos. Patching Smarter Is.
Published: 05/14/2026
Achieving Complete SDLC Visibility and Security in a Multi-Cloud World
Published: 05/11/2026
Anthropic’s Project Glasswing Is a Positive Step Toward Cleaner, Safer Production
Published: 05/05/2026






.jpeg)


.jpeg)