CSA Research
Best practices, guidance, frameworks and tools to help the industry secure the cloud. Read our research to get your questions around cloud security answered.
CSA Research is created by the industry for the industry and is both vendor-neutral and consensus driven. Our research is created by subject matter experts who volunteer for our working groups. Each working group focuses on a unique topic or aspect of cloud security, from IoT, DevSecOps, Serverless and more, we have working groups for over 20 areas of cloud computing. You can view a list of all active research working groups. To find out more about how our research is created and the process we follow you can view the CSA Research Lifecycle.
.png)
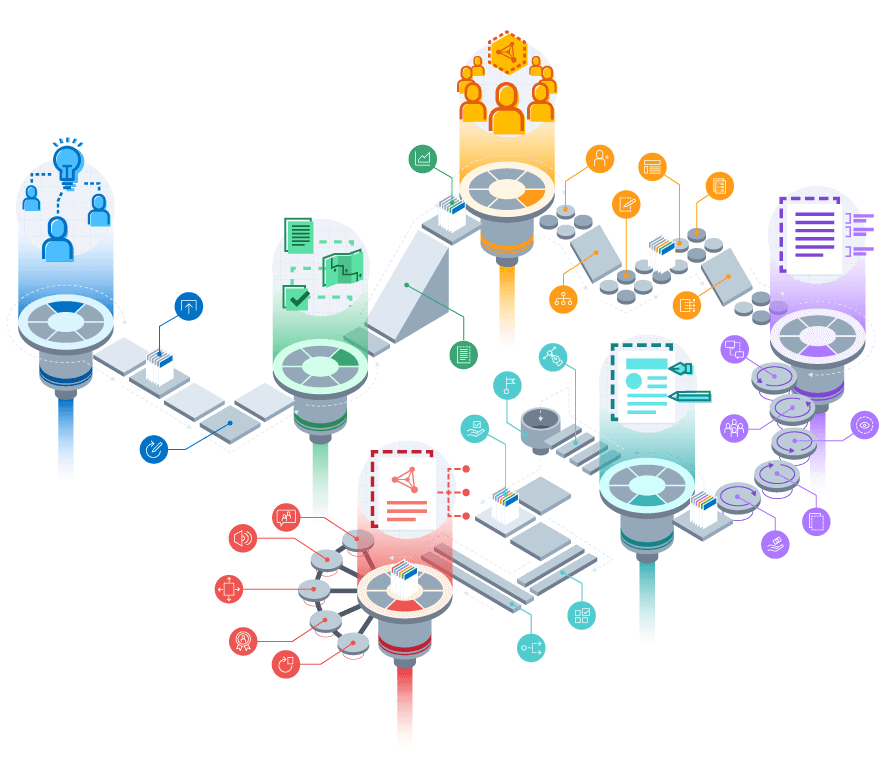
Architectures and Components
Cloud Security Services Management
Enterprise Architecture
Hybrid Cloud Security
Contribute to CSA Research
Peer reviews allow security professionals from around the world to collaborate on CSA research. Provide your feedback on the following documents in progress.
Latest Research
Helpdesk Hijack
Release Date: 06/02/2026
NIST AI Consortium: New TEVV Standards for Enterprise Compliance
Release Date: 06/02/2026
The Presidential AI Executive Order and Industry Alignment
Release Date: 06/02/2026

.png)
.png)
.png)


.png)
