WinRAR CVE-2023-38831 Vulnerability Draws Attention from APTs
Published 12/28/2023
Originally published by Uptycs.
Written by Shilpesh Trivedi and Nisarga C M.
In April 2023, the cybersecurity community faced a significant challenge with the discovery of CVE-2023-38831, a vulnerability affecting versions of WinRAR prior to 6.23. This security flaw has become a critical concern due to its exploitation by various advanced persistent threat (APT) groups, who have used it to gain control of victim systems through deceptive methods.
The methods employed by these APT groups have been notably creative and insidious. They have been exploiting this vulnerability by embedding malicious executables within commonly used file types, such as PDFs and JPGs, within ZIP archives. This tactic allows attackers to install malware on a user's device without arousing suspicion, as the victim believes they are interacting with a harmless file.
The exploitation of CVE-2023-38831 has not been limited to any one region. Instead, it has seen a global spread, with threat actors including APT groups like DarkMe, UAC-0057, APT40, Konni, and SandWorm. These groups have strategically targeted various sectors, including trading, government, energy, and the cryptocurrency industry, across multiple countries.
In this blog, we further describe how each APT group has employed unique tactics to exploit this vulnerability. These tactics range from using phishing emails containing malicious ZIP files to deploying different families of malware, each targeting specific industries and countries.
In addition to the exploitation tactics, this blog provides detailed insights into various types of malware disseminated through this exploit. This includes malware like DarkMe, GuLoader, Remcos, Agent Tesla, PicassoLoader, and Rhadamanthys, each with its distinct functionalities and targets.
Updating to the latest WinRAR version is of critical importance as a mitigation strategy against CVE-2023-38831.
Overview
WinRAR zero-day vulnerability
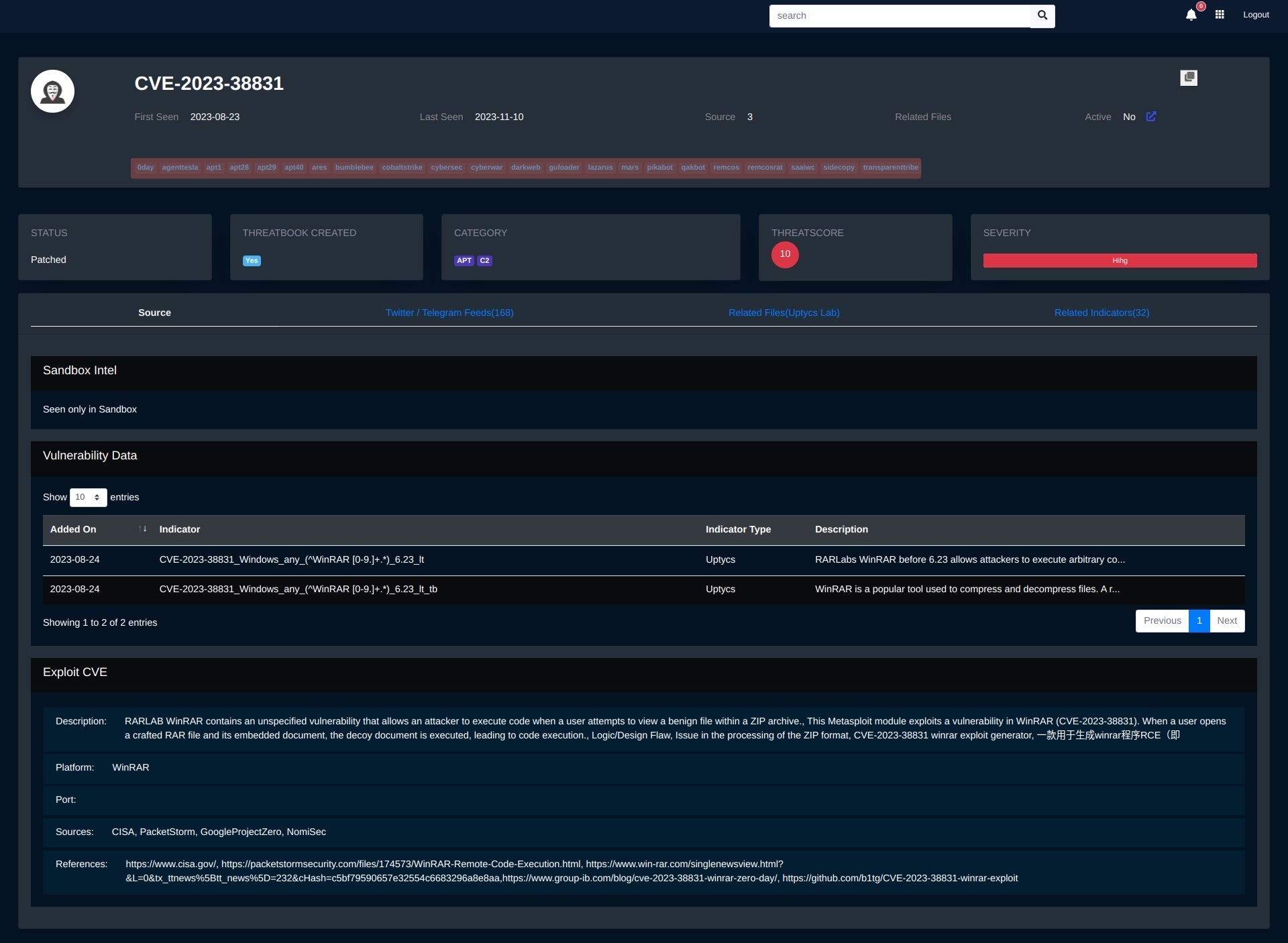
Figure 1 - Threat intel portal : Overview of WinRAR vulnerability
Recently, it has been discovered that the WinRAR vulnerability, tracked as CVE-2023-38831, has compromised its handling of file extensions, giving opportunities for unauthorized code execution.
Uptycs Threat Research Team has outlined the WinRAR vulnerability in a previous blog, detailing its exploitation and providing technical insights.
Interestingly, this vulnerability can hide malicious executables within seemingly benign files, such as .PDFs or .JPGs, in an archive. When a victim double-clicks on the PDF, the vulnerability will quietly launch a script in the folder to install malware on the device. Simultaneously, this script will also display the decoy document so as not to arouse suspicion.
The vulnerability is triggered by creating specially crafted archives with a slightly modified structure, compared to safe files, which causes WinRAR's ShellExecute function to receive an incorrect parameter when it attempts to open the decoy file.
As a result the program bypasses the harmless file and instead locates and executes a batch or CMD script, so while the user assumes they are opening a safe file, the program launches a different one.
Timeline
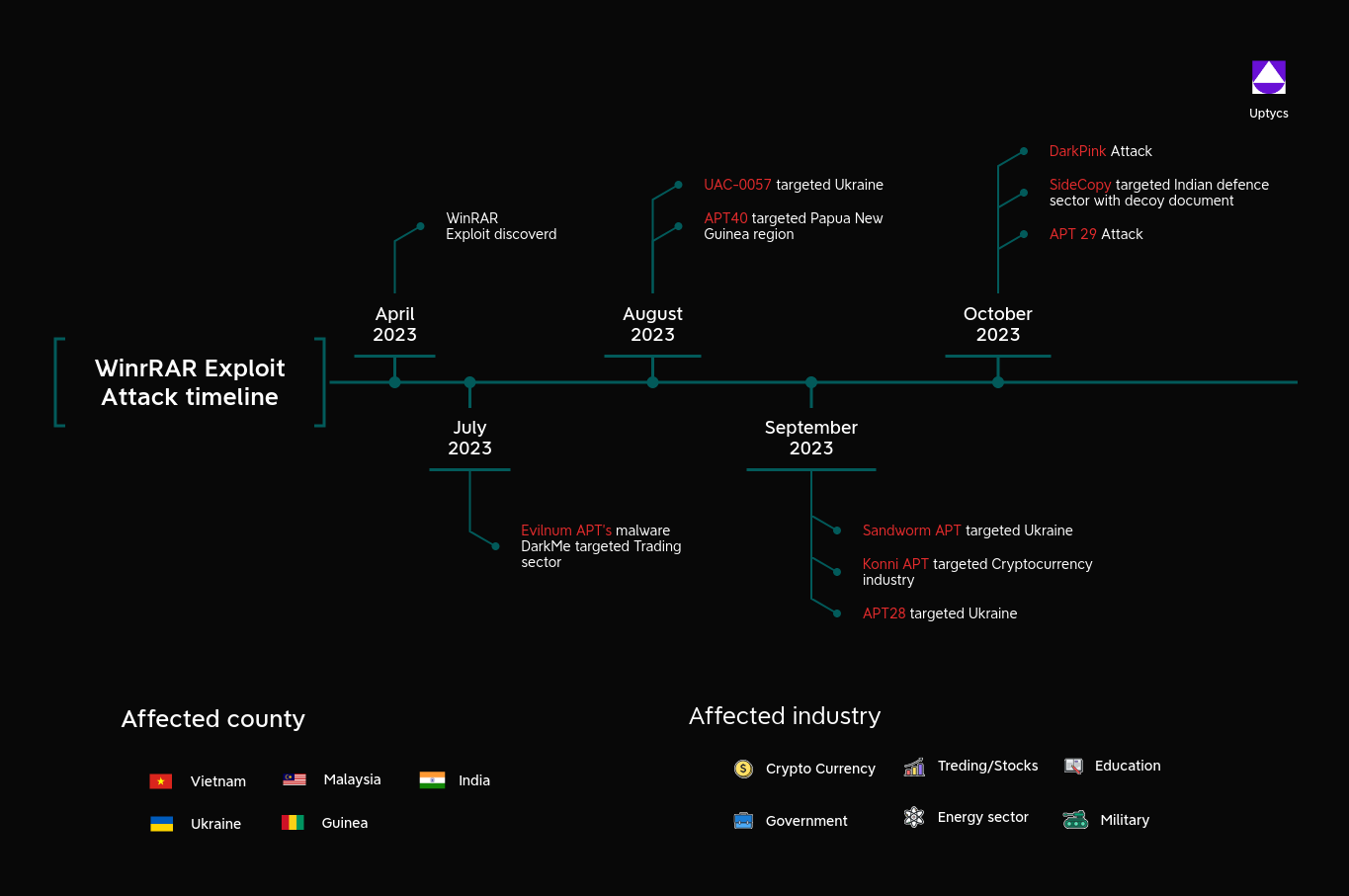
Since April 2023, experts have discovered that the RARLAB WinRAR application before 6.23 contains a zero-day vulnerability. Various threat actors named below have used this vulnerability to deploy attacks on the affected victim's system to gain control of it.
Figure 2 - WinRAR exploit attack timeline
DarkMe – a malware used by Evilnum APT – began exploiting this vulnerability in July 2023, by upgrading their tactics to initiate an attack by employing Zip archives on the targeted Trading sector’s victim system.
In August 2023, the UAC-0057 group, which primarily targets the Ukraine region, has also employed this exploitation technique and ultimately drops PicassoLoader malware through a Cobalt Strike C2 server.
Also in August, the Chinese threat actor named APT40 has targeted Papua New Guinea by launching a phishing email campaign that included a Zip archive file in a legitimate DropBox link. Once opened, the archive file triggers the WinRAR vulnerability to drop their second-stage payload.
In September 2023, attacks from Russian and North-Korean threat actors have been reported by researchers.
The Russian-based threat actors named SandWorm and APT28 have targeted the Ukraine region. Both the actors have targeted Energy sectors.
Sandworm APT targeted a drone warfare training school, utilizing the WinRAR vulnerability in a malicious ZIP archive to drop the Rhadamanthys stealer malware. Meanwhile, APT28 threat actors targeted Ukraine region victims by using a free hosting provider to offer the exploiting WinRAR vulnerability.
Konni – a North-Korean based threat actor – which is rapidly gaining prominence in cyber-espionage activities has also employed the CVE-2023-38831 vulnerability to mainly target the CryptoCurrency industry.
Currently, an actively ongoing cyber campaign is underway, and in Octobe, the DarkPink APT also employed this vulnerability to target the Government sector in Vietnam and Malaysia.
APTs actively exploiting the WinRAR vulnerability
This vulnerability has led to the propagation of various malware families.
DarkPink
In the latest reports, experts have discovered that the DarkPink APT, also known as Saawic, has started using WinRAR zero-day vulnerability to target government sectors in Vietnam and Malaysia.
DarkPink has used a variety of baits. These baits are all in the form of PDF files and placed in WinRAR vulnerability files to attract users to open and view them. The bait file used by the DarkPink APT utilizes real photocopied government documents to increase the deceptiveness of the bait.
The CVE-2023-38831 exploit file built by DarkPink bundles with a pdf bait file and a folder with the same name. The folder contains two files, an exe program with the same name as the pdf bait file and a library file named 'twinapi.dll'.
When a user tries to open a PDF bait file in an earlier version of the WinRAR program, the CVE-2023-38831 vulnerability exploit is triggered, causing the EXE program in the folder to be executed. Later, the EXE program will try to load the 'twinapi.dll' file in the same directory, forming a side-loading attack mode.
The 'twinapi.dll' is a loader type Trojan which is used to extract a piece of data from the PDF bait file, decrypt one of the PE files and inject it into the parent process. The loaded PE file is DarkPink's iconic loader Trojan program "TelePowerDropper'', which ultimately implants the remote control Trojan program "TelePowerBot'' in the victim's host.
Konni
Konni, the North-Korean based threat actor, has reportedly exploited the WinRAR (CVE-2023-38831) vulnerability to target the crypto industry.
Here, in this campaign, the sample file is represented with the name wallet_Screenshot_2023_09_06_Qbao_Network.zip, which refers to legitimate Qbao Network cryptocurrency wallet.
Later, when the victim extracts the archive file and clicks on the html file, which is actually an EXE file that upon executing it initiates a thread to employ the GetSystemWow64DirectoryW function to detect whether the current system is 64-bit
Once confirmed, Konni actors start downloading a final payload by contacting its C2 server.
Then it starts collecting the system information, and finally shares back to its attacker-controlled server.
SideCopy
A Pakistan-based APT named Sidecopy has also used the similar-kind of techniques as other reported threat actors on using WinRar exploitation, but here the actors target specifically on the Indian defence sector that pretend as AIANGOs [All India Association of Non Gazetted Officers].
The bundled zip file contains 1 benign PDF file and one folder with EXE file which are both named as Achievements_of_DMF.
Upon running on EXE file, it tried contacting its command-and-control server vmi1433024[.]contaboserver[.]net. Upon further analysis, it has been discovered that this malicious domain is responsible for dropping the Remote Access Trojan [RAT] payloads.
APT29
APT29, also known as CozyBear, Nobelium, The Dukes, has used the WinRAR vulnerability, to target the Europe victim’s with the malicious zip archived file containing PDF and bundled images and BAT file in the same name DIPLOMATIC-CAR-FOR-SALE-BMW.
Here, APT29 has shifted their tactics to trigger the vulnerability from the BAT script file, whereas other threat actors have used the EXE file in some cases.
Once running the BAT file, it tries to download the PowerShell file, with the URLs
hXXps://d287-206-123-149-139[.]ngrok-free[.]app/b125[.]ps1 and hXXp://d287-206-123-149-139[.]ngrok-free[.]app:443.
For further analysis as we checked, both the URL’s were inactive.
However, by finding this, it has been discovered that threat actors are using Ngrok platform for its malicious activity.
UAC-0057
At the end of August, the UAC-0057 threat group started exploiting the CVE-2023-38831 vulnerability which was archived in the RAR file.
Upon exploiting the successful vulnerability, it leads to BAT file execution, which pretends to be a PDF file. Upon clicking the file, it launches an LNK file by using Mshta.exe utility that leads to the execution of the HTA file.
Later, this leads to the execution of JavaScript code to download a crafted image file that targets the victim system by Cobalt Strike bacon. This ultimately causes dropping the final PicassoLoader malware.
APT28
Russian group, APT28 has also initiated an attack by involving the use of malicious archive files that exploit the vulnerability CVE-2023-38831 affecting the WinRAR compression software versions prior to 6.23.
In one of the campaigns, the attack is initiated through the crafted HTML page to target the Ukraine Energy sector victims. Here, it was prompting the victim to download a malicious document file which is responsible for exploiting the WinRAR vulnerability.
In another case, through the WinRAR CVE-2023-38831 exploit, it drops a BAT file.
Upon executing this BAT file, it opens a decoy PDF file and creates a reverse SSH shell to an attacker controlled IP address, and finally executes IRONJAW script using PowerShell.
It's a small PowerShell script that can be used to steal browser login data and local state directories, and helps in exfiltrating the collected details to their C2 server.
SandWorm
SandWorm group, attributed to Russian Armed Forces’ Main Directorate of the General Staff (GRU) Unit 74455, has recently launched an email campaign impersonating a Ukrainian drone warfare training school.
Here, in this campaign, the threat actors trick the victim by an invitation-themed email to join their academy. The emails contained a link to download a decoy PDF file with the malicious ZIP file.
The ZIP archive file is bundled with the CVE-2023-38831 exploit that is executed via the BAT file. Ultimately, the BAT file drops a recent-active infostealer payload named Rhadamanthys.
APT40
APT40, a chinese-government-backed threat actor, also started in late August 2023, by launching a phishing campaign targeting Papua New Guinea.
The email included a Dropbox link to a ZIP archive containing the CVE-2023-38831 exploit, a password-protected decoy PDF, and an LNK file.
Later, an XOR-encoded DLL payload named ISLANDSTAGER has been found at a hardcoded offset inside of the LNK, or downloaded from a hardcoded URL of a file-sharing service.
Then, ISLANDSTAGER will execute and make sure to configure its persistence by modifying the registry key. Later, once decoding the shellcode, it loads and executes the final BOXRAT backdoor payload that makes use of Dropbox API as a C2 server.
Malware delivered via the WinRAR vulnerability
CVE-2023-38831, the WinRAR zero-day remote code execution vulnerability, has been exploited in the wild to distribute several malware families such as:
DarkMe
An identified suspicious activity of DarkMe - a malware used by Evilnum APT - employing their initial attack tactics to Zip archive files, has prompted researchers to investigate those archive files and found that its been exploiting WinRAR vulnerability to take its advantage by targeting the Traders sector, which often focused by Evilnum APT to target Finance sector.
Once the crafted ZIP archives reached the affected systems, the malware payloads contained inside the archives were executed, leading to their devices being compromised.
Threat actors had exploited this vulnerability to spoof the file extensions, to hide the launch of malicious code within an archive masquerading as a '.jpg', '.txt', or any other file format.
The launch process for DarkMe is complex and involves multiple modules. In this case, the malicious coded script launches the Cabinet Self-extractor file, also known as an SFX CAB file.
The archive contains 5 files, and one of the main execution files named 'cc.exe' plays a crucial role by initiating various malicious modules. This will be launched after extraction and finally, it kills itself and launches the "DarkMe" backdoor using the RunDLL command.
Guloader
In one instance, researchers found ZIP variants that used NSIS installers instead of SFX archives. Here, in this campaign activity, the NSIS package starts the launch by running the PowerShell script stored in the file named 'Piskens.For187', which is inside the package.
The process also includes decrypting and running another stage, leading to the launch of GuLoader malware.
As researched, the GuLoader also attempts to get to the next stage by making an HTTP request using the malicious URL.
According to the reports, threat actors used this domain between April 17 and July 18, 2023. After the payload is downloaded and decrypted, Remcos RAT is executed.
Remcos
Remcos is a type of remote access Trojan that facilitates unauthorized remote control and surveillance of compromised systems. The malware is designed to infiltrate computers, gain control over them, and exfiltrate sensitive data.
It is primarily spread through malicious attachments or social engineering tactics.
On October 9th, it was discovered that Remcos RAT had been dropped by using the WinRAR exploit CVE-2023-38831 by threat actors to target the Ukraine government sector in the name of NATO-zip archive file, bundled with benign PDF File and cmd file to drop the Remcos RAT payload.
Agent Tesla
Threat actors have been found spreading the Agent Tesla malware by making use of CVE-2023-38831.
Within a folder with the same name, a CMD file was hidden as a PDF file. When this file is clicked, the Agent Tesla malware is launched.
Picassoloader
Named UAC-0057, the Russian-state sponsored actor, has been started using the CVE-2023-38831 vulnerability in a Zip archive that was circulated through phishing email.
The zip archive is bundled with JPG images and a BAT file named with .cmd extension.
Upon running the cmd file, multiple VBS and Bat. files are created and launched to deploy the next-stage of malware named PicassoLoader malware to target the Ukrainian critical energy sector.
Rhadamanthys
Rhadamanthys is an infostealer malware which has the capability to collect and exfiltrate browser credentials and session information, among other things. Rhadamanthys is also capable of extracting credentials of various applications such as Keepass and cryptocurrency wallets.
In the reported campaign, the Sandworm APT targeted the Ukraine region via a phishing email campaign with attached malicious ZIP archive file.
The ZIP file is bundled with a PDF and BAT file with the same name. The BAT file triggers the CVE-2023-38831 vulnerability to drop the final Rhadamanthys payload infostealer.
IRONJAW
APT28 actors have exploited WinRAR vulnerability CVE-2023-38831 to drop a BAT file which opens a decoy PDF file and creates a reverse SSH shell to an attacker controlled IP address, and executes IRONJAW script using PowerShell.
IRONJAW is a small PowerShell script that steals browser login data and local state directories, exfiltrating them to their C2 server.
Multiple other malware has also been spotted in exploiting such campaign activity such as BumbleBee, WhiteSnake stealer, njRAT trojan, BOXRAT backdoor and few command-and-control frameworks such as Cobalt Strike and Mythic Agent.
Shifting tactics, techniques and procedures (TTPs)
As per the analysis, threat actors have continuously shifted their tactics to improvise their attack campaign to successfully target the victim system to exploit a WinRAR vulnerability.
At first, the DarkPink actors initiated an attack with Phishing mail to drop an RAR archive file with CVE-2023-38831 exploit appended in the file. And for the persistence methodology, it performs UAC bypass by the dropped EXE file with DLL side-loading injection mechanism.
Later, it connects to its command-and-control server for sending the collected system information.
Later, in Konni APT campaign activity, it performs the same pattern of attack except using BAT script file instead of EXE file.
Few other threat actors like UAC-OO57, SideCopy, APT28 exploit WinRAR vulnerability with CMD [Command-and prompt] file to drop LNK file with MSHTA utility to access malicious HTML [HTA] file that is injected with malicious JavaScript code to drop a final payload.
Now in the recent campaign activity, multiple russian threat actors like APT29 uses PowerShell script, once triggering an exploit from a BAT file, to drop the final payload by contacting its C2 server.
Attack insights
Threat actors from countries like North Korea, Russia, Pakistan, and China exploit this vulnerability to target nations or industries.
Attacking countries
The depicted figure below highlights the geographical regions of threat actors and their frequent utilization.
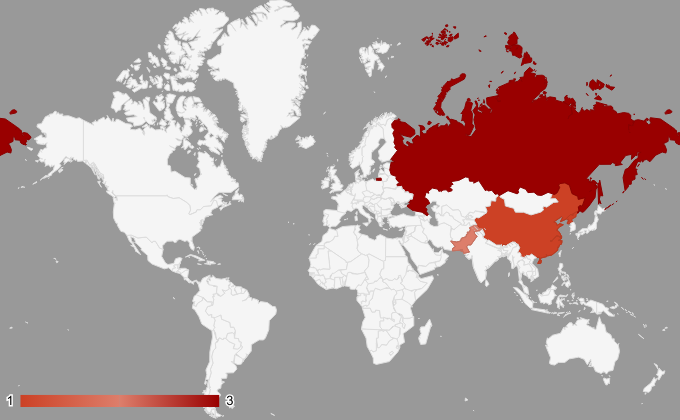
Figure 3 - Offending APT nations
| Country Name | Associated Threat Actors |
| North Korea | Konni |
| Russia | Sandworm APT 29 APT 28 |
| Pakistan | SideCopy |
| China | APT40 |
Hunting queries
By performing the following hunting SQL query, we can get the WinRAR vulnerability details.
To find the malware based on the WinRAR vulnerability, log in to Uptycs Stack, navigate to the Investigate page, and paste the following query:
select * from process_events where ((exe_name = 'cmd.exe' OR exe_name = 'powershell.exe' OR exe_name = 'powershell_ise.exe' OR exe_name = 'wmic.exe' OR exe_name = 'rundll32.exe' OR exe_name = 'mshta.exe' OR exe_name = 'explorer.exe' OR exe_name = 'cscript.exe' OR exe_name = 'wscript.exe' OR exe_name = 'javaw.exe' OR exe_name = 'WmiPrvSE.exe' OR exe_name = 'schtask.exe' OR exe_name = 'reg.exe' OR exe_name = 'regsvcs.exe' OR exe_name = 'regsvr32.exe' OR exe_name = 'at.exe' OR exe_name = 'certutil.exe' OR exe_name = 'msbuild.exe' OR exe_name = 'psexec.exe' OR exe_name = 'curl.exe' OR exe_name = 'wget.exe') OR (cmdline like '%AppData\Local\Temp\Rar$%' AND cmdline like '.') AND ancestor_list like '"exe_name":"winrar.exe"') AND (exe_name != 'conhost.exe' AND exe_name != 'werfault.exe')
Indicators of compromise
Hash
5716244ce0f3bbae24b79db810e80cd5001b320e6608a838284b22889143ca66 | SideCopy |
5893b58d6a6a772f8ecd491a4dace11007fd1aac90e5f4a0363288d1376e1ce5 | |
eec902a61886198a8e48ac862fabeecd628f2fa4122b78a0d7d6ee5c256ae724 | APT29 |
f78ee3005ca9f0e78a9dd136fc69afe7c06d69d1fc6218bc9e7eb3adec045977 | |
5d6bfb8fd1102273ef489060219293f8da796d07e8b2872efbda55050512b71f | |
378f6ec865c7ed29742d0b8f156e7171cde8b7fc25c2ccfca21abc77cca5aa83 | DarkPink |
a9da81172425d580b53b72b559f7ec8f496ded783b40e012c77f6cb669405068 | |
3cf0408ce29f916beb1fc5767a028c0f8c7dd4c0311002e0827f7557c0c25ab4 | |
40d1ebcca7ed35da9776383abca3e7ec6b70aec53c739aef773cdb90726f46c0 | |
42b4be54955f9e17b7135ef34bb924874045ed4fde51bbe7fa33e67acd3a699a | |
173ec2775bfb01977985303863af2a7218e5ead7cf2592e971b99bdd91a850e9 | |
35f42a0fb17fa9e7d32e47df859a2b8239f236b1b2baf51f5b33963e728ea5d4 | BumbleBee |
60f4f1cd1eed873c414fb56441a3d76efbb469ee1312b3b73c0534eec1e082d3 | |
79a4fa2ac4971f669cbcbe4f1573bbc893f05490a9a0d0d9d6b6c1c91bb3a1c4 | Remcos RAT |
6ca54ba5f6665ddf1653cc3564647918eaa5290045dfca20b30235d73d0ebd99 | |
3e92abb85fe234dd55668fc71346164ef3a65051ddeff8b4d871837300b03878 | AgentTesla |
15a4c64ec2cdc0f9b77763c7ad7b0181e5852ed5e74d1090e6112a9f05d34e8a | |
c5b392748985dc71aea2ea1a54e59ae68d90c43c0de44dfdf7f6b55c65d99540 | Exploit samples |
| 74bc4c892f5590610c31057c4f60d6f7e1d7fafff4565d5726d82ef262888632 |
Domain
vmi1433024[.]contaboserver[.]net | SideCopy |
d287-206-123-149-139[.]ngrok-free[.]app | APT29 |
g7qf7ew5c[.]life | BumbleBee |
IP
45[.]142[.]212[.]34 | C2 Indicators |
| 38[.]242[.]149[.]89 |
MITRE techniques used on WinRAR exploitation
On overall analysis of the threat actors used the below MITRE Framework Techniques to exploit the severe WinRAR vulnerability to perform an attack.
Tactics | Techniques |
Initial Access | T1566 - Phishing |
Execution | |
Execution | T1059 - Command and Scripting Interpreter |
Persistence | T1574 - DLL Side-Loading |
Persistence | T1205 - Traffic Signaling |
Privilege Escalation | T1548.002 : Bypass User Account Control |
Defense Evasion | T1112 - Modify Registry |
Credential Access | T1555.003 - Credentials from Web Browsers |
Discovery | T1082 - System Information Discovery |
Lateral Movement | T1563 - Remote Service Session Hijacking |
Collection | T1560 - Archive Collected Data |
Command and Control | T1071 - Application Layer Protocol |
Command and Control | T1105 - Ingress Tool Transfer |
LOLBINS used
LOLbins Utility | Techniques |
Mshta.exe | T1218.005 - Mshta |
Cmd.exe | T1059 - Command and Scripting Interpreter |
PowerShell.exe | T1059.001 - PowerShell |
WScript.exe | T1059.005 - Visual Basic |
RunDLL32.exe | T1574.002 : DLL Side-Loading |
YARA rule
rule Uptycs_CVE_2023_38831_PK_FILES
{
meta:
malware_name = "CVE-2023-38831"
description = "CVE-2023-38831 is a vulnerability that enables malicious actors to execute
arbitrary code when a user tries to access a harmless file contained within a ZIP
archive."
author = "Uptycs Inc"
version = "1"
strings:
$magic_header = "PK" ascii
$string_pattern = /(.{1,256}\.[A-Za-z1]{2,4})\s\/(.{1,256}\.[A-Za-z1]{2,4})\s\.
[A-Za-z0-9]{2,4}/
condition:
$magic_header at 0 and $string_pattern
}
Credits: Thanks to our Uptycs Threat Research team members Dinkar Jaiswar and Rishabh Kachhara for maintaining and making enhancements with the threat intelligence portal for identifying the latest attacks and threats.
Unlock Cloud Security Insights
Subscribe to our newsletter for the latest expert trends and updates
Related Articles:
Code-to-Cloud Security: Embracing a Unified, Ecosystem-Wide View of Cyber Risk
Published: 03/30/2026
Control the Chain, Secure the System: Fixing AI Agent Delegation
Published: 03/25/2026
Securing the Agentic Control Plane: A New Foundation for Trust in AI
Published: 03/20/2026





.jpg)



