This localized version of this publication was produced from the original source material through the efforts of chapters and volunteers but the translated content falls outside of the CSA Research Lifecycle. For any questions and feedback, contact [email protected].
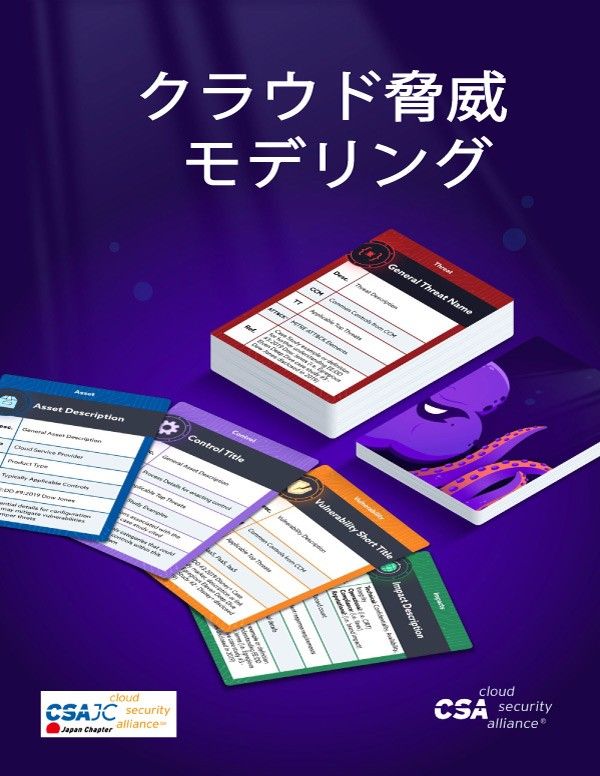
Threat modeling serves to identify threats and preventive measures for a system or application. However, threat modeling is one security methodology that has not matched the general rate of cloud adoption, due to a gap in guidance, expertise, and applicability of the practice. Threat modeling for cloud systems expands on standard threat modeling to account for unique cloud services. It allows organizations to further security discussions and assess their security controls and mitigation decisions.
この出版物の翻訳版は、CSA日本支部とボランティアによって原本から作成されましたが、翻訳されたコンテンツはCSA Research Lifecycleの範囲外です。質問やフィードバックについては、[email protected]にお問い合わせください。
この出版物の翻訳版は、CSA日本支部とボランティアによって原本から作成されましたが、翻訳されたコンテンツはCSA Research Lifecycleの範囲外です。質問やフィードバックについては、[email protected]にお問い合わせください。
脅威モデリングは、システムまたはアプリケーションの脅威と予防策を特定するのに役立ちます。しかしながら、クラウドシステムにおける脅威モデリングが軽視されている主な要因は、ガイダンス、専門知識、プラクティスの適用性にギャップがあることです。クラウドシステムの脅威モデリングは、クラウドサービスを説明するために標準の脅威モデリングを拡張しています。 これにより、組織はセキュリティに関する議論をさらに進め、セキュリティ管理と緩和策の決定を評価できます。
Download this Resource
Prefer to access this resource without an account? Download it now.