CSA Research Lifecycle
A Standardized Process for Developing, Validating, and Publishing CSA Research
Released: 05/28/2026
Use this resource to align with CSA’s research process, download the lifecycle for reference, or submit research ideas to [email protected].
Download this Resource
Prefer to access this resource without an account? Download it now.
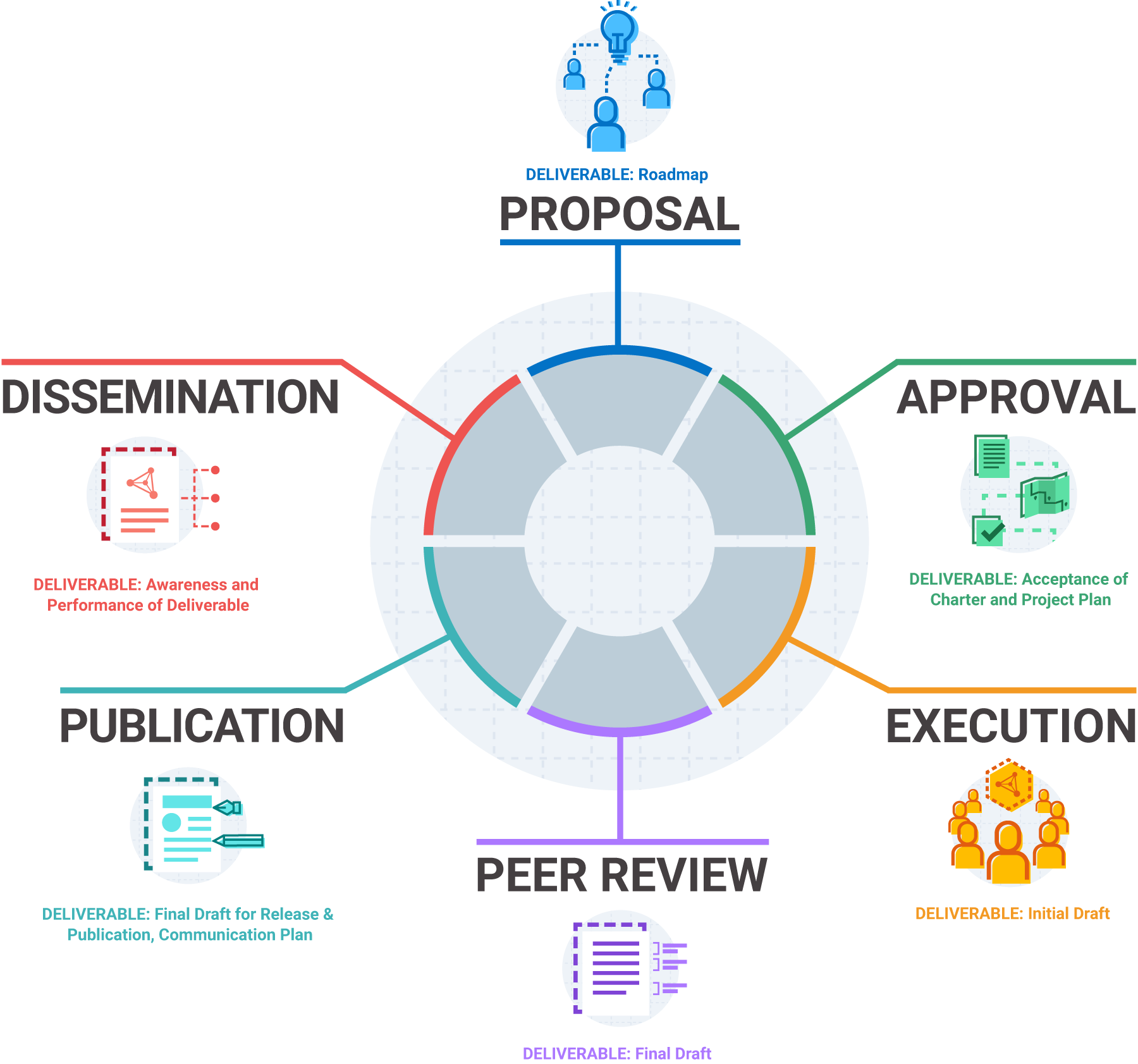
Figure 1: Stages in the CSA Research Lifecycle
1. Proposal
Cloud Security Alliance initiatives and projects are conceived and proposed through
discussions, submissions, and current trends. New ideas are submitted as research
proposals to the appropriate working group(s) or CSA executive team for continued
development and discussion by members and professionals alike. Research proposals
are selected as a consensus by the working group as relevant to the community or
industry needs.
- Timeline: 1-4 months
- Deliverable: Roadmap
Steps in the Proposal stage:
- Submission: New ideas or revisions are submitted through various CSA channels by individuals or members of existing CSA Working Groups.
- Review: Ideas are vetted by the CSA Research and Executive team and reviewed by the appropriate working group(s) or select third parties (e.g. Industry Specific Associations, SDO’s, Affiliate Partners, Corporate Members) when applicable.
2. Approval
Overview of work (working group charter, project plan, roadmap, etc.) is developed or updated by members of the working group and are submitted to CSA advisory groups for review and approval.
- Timeline: 1-4 months
- Deliverable: Acceptance of Charter and Project Plan
Steps in the Approval stage:
- Statement of Work: Develop and/or update a working group outline to define scope of work and high level milestones for the proposed body of work.
- Evaluation: Internal strategic evaluation by one or more of CSA advisory groups and select industry groups.
3. Execution
Research is approved and/or official working group is formed. Appointed leadership carries out research in a collaborative and transparent environment. Plans are developed, and deliverables and key milestones are identified. Meetings are set and research begins.
- Timeline: 4-12 months
- Deliverable: Initial Draft
Steps in the Execution stage:
- Call for Contributors: Determine resource needs and announce a call for participation
- Leadership Appt.: Project roles and responsibilities defined. Subgroups formed if necessary.
- Project Planning: Development of work package, references, tools, communication cadence, and platform.
- Research Tools.: As appropriate, set up a collaboration site, CSA Microsite, and email list for communications.
- Content Development: Host calls and working sessions to develop and produce content for deliverable.
- Content Highlights: Bulletpoints to share with Membership, Marketing, and PR for a high-level overview of the document.
4. Peer Review
The peer review process will be conducted to include the internal subgroup(s), working group(s), advisory groups, CSA community, and public sources.
- Timeline: 1-3 months
- Deliverable: Final Draft
Steps in the Peer Review stage:
- Working Group Peer Review: Draft of research artifact is sent to the working group for peer review.
- CSA Peer Review: CSA peer review from Advisory Councils. Outreach begins for draft review by Marketing and PR.
- Open Peer Review: Draft is released to the public for industry feedback.
- Incorporate Feedback: Compilation and deliberation of feedback into research artifact. (1 week minimum)
- Sponsorship Outreach: Develop sponsorship proposal outlining details within agreement. Determine timelines with PR and Sponsors and other ramifications. (if applicable)
5. Publication
The publication phase involves copyediting, formatting, and final internal review of artifacts prior to publication.
- Timeline: 1 month
- Deliverable: Final Draft for Release & Publication, Communication Plan
Steps in the Publication stage:
- Production: Final artifact is sent to design for formatting, copyediting, and copyright protection. Website URLs are created. Additional assets are created, if necessary. (Three weeks prior to publication)
- Final Review: Final review and approval by Research.
- Finalize Sponsorship: Finalize sponsorship and design assets, if applicable. Distribute marketing information on how to maximize alliance with CSA.
- Early Access: Share and Distribute to CSA members at least week before Publication date.
- Distribution Plan: Publication process to include PR, addressing and target channels for promotion and marketing of release and final updates to prepare for publication. Early access determined for release.
6. Dissemination
Promotion and assessment of artifact adoption.
- Timeline: Ongoing
- Deliverable: Awareness and Performance of Deliverable
Steps in the Dissemination stage:
- Publish: Artifact posts to standard communication channels such as social, online, and email lists.
- PR Promotion: Promote through internal and external marketing and PR programs.
- Continued Distribution: Promotion through CloudBytes webinar, sponsor hosted events, speaking opportunities for SMEs, social media announcement, etc.
- Volunteer Recognition: Emphasize and highlight volunteers and contributors through social media and other announcements.
- Research Evaluation: Review the publication analytics and repeat research lifecycle as necessary to revise and update content. Release new versions of research material.



