- The critical differences between identity spoofing and identity abuse
- How to apply Zero Trust principles to strengthen identity security and access control
- How to implement risk-based, context-aware authentication and monitoring
- Common weaknesses in identity ecosystems
- How to prepare for emerging threats, including AI-driven identity attacks
Download this Resource
 Best For:
Best For:
- IAM Architects
- Security Architects & Engineers
- SOC Analysts
- Information Security Managers
- Risk & Compliance Professionals
- Network & Cloud Security Engineers
Spoofing and Abusing Identities
Note to the reader: When the Zero Trust Identity Pillar Working Group started work on how identity is misused by bad actors, it became clear that their methods fell into a clear taxonomy of two classes of misuse—identity spoofing and identity abuse—where the methods of misuse, and thus the method used to detect and protect, were fundamentally different.
Abstract
The shift towards Zero Trust architectures brings in a heightened focus on the integrity of identity and identity attributes. In a world where traditional network perimeters are increasingly irrelevant and a hybrid way of working is the norm, long established security models prove to be inadequate.
The Zero Trust strategy is built on the principle of “never trust, always verify.” This principle places an immense reliance on the continual authentication using accurate and reliable identity attributes from all the entities in the communication chain. This principle also relies on the validation of the integrity of other signals used to provide confidence.
As the cornerstone of access control decisions, the authenticity and completeness of identity attributes, the entities that sign/validate them, and the confidence in other signals (including but not limited to IP addresses, location, and device security) become paramount. Thus, any compromise in the integrity of identity, identity attributes, or signals can lead to consequences, including data breaches, unauthorized access, and reputational damage.
This paper looks at how the identity ecosystem can be subverted by malicious actors with identity spoofing, where an attacker assumes the identity of another entity—real or fictitious—to abuse the attributes of an existing entity, which are stolen or subverted. The paper also examines risk-based prevention and mitigation strategies that can be adopted to increase security confidence, awareness, and proactiveness.
Target Audiences
Primary Audience: Identity and Access Managers (IAM) and Architects, Information Security Managers and Architects, and Security Operations Center (SOC) Architects and Analysts
Secondary Audience: Auditors, Information Security Regulators, IAM Practitioners, Security Engineers, and Network Operations Center (NOC) Architects and Analysts
Scope
This paper explores the concepts of spoofing of identities and abuse of identities, which are attack techniques where malicious actors disguise communication and identities from an unauthorized source as being from an authorized, trusted source. It delves into the origins of spoofing while examining how these attacks are initiated and the methods used to deceive victims. The paper also discusses the various ways in which identities can be abused in the digital realm, including phishing, social engineering, and identity theft. Furthermore, the paper analyzes the implications of these threats within the framework of the Zero Trust Architecture, which operates on the principle of “never trust, always verify,” emphasizing the need for continual verification of identities and access controls to reduce the risks associated with identity spoofing and abuse.
.png)
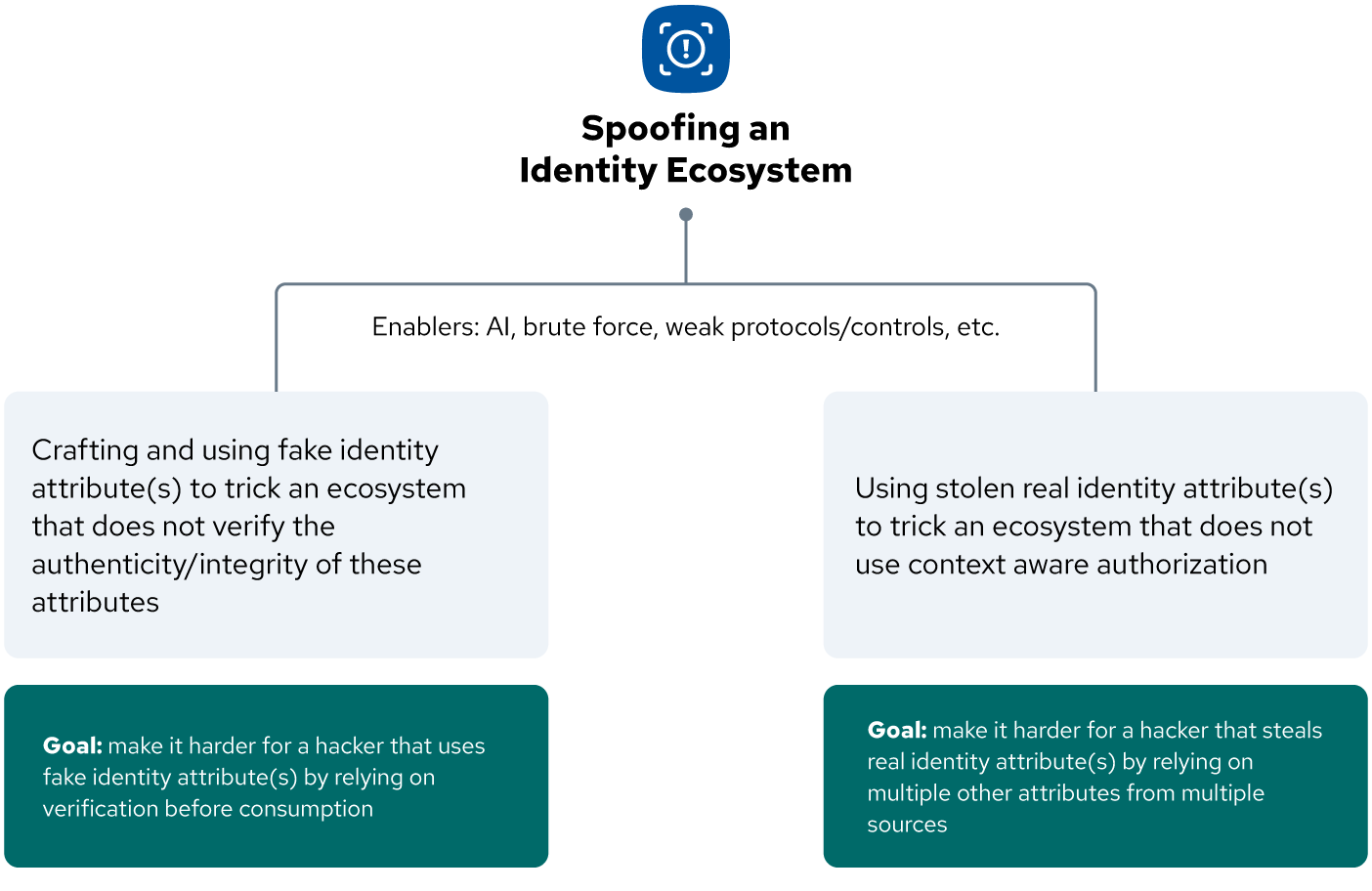
Figure 1: Spoofing Identity Ecosystems (Raouda, 2025)
Introduction
While both identity spoofing and identity abuse refer to the misuse of identity, the risks and controls of these two classes are fundamentally different.
Identity Spoofing
Masquerading as a fictitious entity—also known as impersonation, deception, or forging.
Examples would be:
- The creation of a fake social media persona of a US citizen by a foreign entity intent on using it to spread disinformation
- Creation of a domain name like microsoft-2fa.com, which is not a Microsoft domain
- Creation of an email like [email protected], which is not an Amazon email
- Registering for a passport using information from a deceased person
Identity Abuse
The theft and fraudulent use of an existing identity, persona, or attribute(s), allowing the malicious actor to act as that entity.
Examples would be:
- Account takeover, where a malicious actor gains access to an existing account
- Domain takeover, where a malicious actor gains access to domain records and can redirect email, websites, and so on
- Fraudulently using an existing identity to:
- open a new account, make unauthorized purchases, or take out loans
- obtain medical services or prescription drugs
- access and control someone’s existing accounts (e.g., bank, email, social media)
- Using legitimate attributes to fabricate a new identity using a combination of real and fake information (synthetic identity)
- Using stolen credentials of a service account used for logging into servers with the same permissions and privileges as the service account
- Performing an Application Programming Interface (API) replay attack using stolen API credentials
- A human user assuming the role of an AWS lambda function, accessing a DocumentDB database, and downloading a commercially sensitive file
The Need for Differentiation
Note to reader: The team felt there is a fundamental misunderstanding by many IT and security professionals around identity, with terms such as Entity, Identity, Persona, Attributes, Assertions, and Trust often being misused or (incorrectly) used interchangeably. (See Glossary.)
The point applies when identity is being discussed, with a focus on only human-related identity problems and solutions rather than those related to non-human identities (NHIs). Ideally, the issues, risks, mitigation, and architectural solutions should consider the identity, persona, and attributes of all entities as a common problem as, over the internet it’s becoming increasingly difficult to distinguish human from non-human!
By considering it as “all just identity,” we end up with a taxonomy that leads to blind spots; however, by classifying the nature of the misuse into the two classes of “spoofing” and “abuse,” we can consider the two fundamentally different attack paths as well as the different detection and mitigation strategies for each class.
Identity Spoofing
Spoofing is a security term that refers to the act of disguising a communication or identity as coming from a known, trusted source. This deception is typically used to gain unauthorized access to systems, steal data, or spread malware.
Overview of Identity Spoofing
Spoofing is an ancient tactic, found not only in cybersecurity but mirrored in nature itself—much like how certain animals adapt their colors and alter their physical structure to deceive predators, evade threats, or lure their prey.
At its core, spoofing aims to deceive an entity (a person, system, or process) through exploiting its identification, authentication, authorization, or verification mechanisms. Cybercriminals and other threat actors often will use spoofing as a common technique to gain unauthorized access to systems, data, and accounts by impersonating a legitimate entity, such as a user, a device, or a network, or by falsifying or manipulating information that is used for authentication or verification.
Not all spoofing is malicious; typosquatting to a “joke” website or making a router identify as a different make and model to foil automated attacks are just two examples.
Examples of Identity Spoofing
-
Email Spoofing: Sending emails with a fake sender address to trick recipients into revealing personal information, opening a malicious attachment, or clicking on a phishing link
-
Caller ID Spoofing: Displaying a false phone or SMS number on a caller ID to mislead recipients
-
Website Spoofing/Domain Spoofing: Creating fake look-alike websites that mimic the legitimate website to steal login credentials via counterfeit login pages
-
Social Media Spoofing: Creating fake social media profiles that impersonate trusted contacts or brands to deceive users into sharing sensitive information, directing them to spoofed websites, or tricking them into buying counterfeit goods
-
IP Spoofing: Sending network packets with a forged source IP address to deceive network devices
-
ARP Spoofing: Poisoning the ARP cache, which can be used for man-in-the-middle attacks or initiating a DDoS attack
-
MAC Spoofing: Changing the media access control (MAC) address of a device
-
Voice Over IP (VoIP) and Session Initiation Protocol (SIP) Spoofing: Mimicking legitimate phone numbers or IDs to conduct social engineering attacks; often using these techniques in vishing (voice-call phishing) campaigns
-
Typosquatting: Mimicking legitimate mobile apps, NuGet packages, npm packages, and so on
-
Sock Puppets: Creating a fake identity for malicious or nefarious purposes
-
GPS Spoofing: Transmitting false or altered signals to interfere with the global positioning system (GPS)
-
Biometric Spoofing: Creating fake or altered biometric samples, such as fingerprints, face images, or voice recordings to fool biometric recognition systems
-
Spoofing Human Personas Using AI: A well known example is the KnowB4 security breach
-
Dynamic Link Library (DLL) Search Order Hijacking: Placing a malicious DLL with the same name as a legitimate one in the search path, allowing it to be loaded by a trusted application
-
Masquerading: Where file names, file types, or even system commands are altered to appear as legitimate system files, documents, or services with users tricked into executing harmful code
-
Domain Fronting: Where the true destination of an HTTPS request is hidden by making it appear to be directed to a legitimate, commonly used domain (the “front” domain), while the actual destination, often blocked or malicious, is specified in an encrypted part of the request
Please note:
- While the signals that participate in the Zero Trust entitlement process may also be spoofed, this is outside the scope of this paper
- Specific attacks such as phishing, spearphishing (targeted phishing), vishing (voice-call phishing), and social engineering attacks, such as Business Email Compromise (BEC), often use spoofing to impersonate an entity (e.g., person, organization) but is much more effective when a genuine account can be compromised (i.e., identity abuse), thus lending credibility to the request
Real-World Examples of Identity Spoofing
To put identity spoofing in context, here are some real-world examples:
-
Business Email Compromise (BEC): Between 2013 and 2015, Evaldas Rimasauskas defrauded Google and Facebook of over $100 million by impersonating an employee of a legitimate Asian manufacturer that both companies worked with to send fake invoices for services1
-
Website Spoofing: Scammers created fake websites that looked almost identical to a legitimate PayPal login page[^2]
-
Caller ID Spoofing (Vishing): Scammers tricked a mother into believing her child was abducted by using AI-generated audio of her daughter screaming in distress and playing it over the phone[^3]
-
SMS Spoofing (Smishing): In 2024, the customers of the Texas Department of Transportation were targeted by a smishing scam claiming they had unpaid toll invoices2
-
Brand Impersonation: In Q3 2024, Microsoft was the most imitated brand in phishing attempts, exploiting Microsoft’s widespread use of services like Outlook and Office 365 to send fake account alerts and login requests3
Controls Against Identity Spoofing
Detective Controls
Because identity spoofing relies on creating a new identity (or persona), the primary detective controls are looking for and spotting anomalies in IP addresses, domains, and headers. Using the Zero Trust principle of comprehensive visibility, the below mentioned inspections support detecting spoofing attacks in real-time or near real-time. The principle of logging all security events and monitoring for anomalies enables an organization to detect unusual behavior, which may indicate spoofing attacks.
-
IP Address and Network Traffic Analysis:
- IP Source Validation: Checking that only trusted IP addresses are sending network queries or accessing systems and detecting unusual IP addresses that don’t belong to the legitimate sender
- Packet Inspection: To analyze network packets for anomalies, such as mismatched IP addresses in headers, which can indicate IP spoofing
-
Email Analysis:
- Look for mismatched “From” addresses (and other mismatched headers) and actual sender domains
- Look for missing or incorrect email authentication protocols like Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication Reporting and Conformance (DMARC), which help verify sender identity
- Alerts on images or other embedded items linked to a different domain
-
Monitoring DNS Traffic:
- Unusual DNS requests can indicate DNS spoofing or cache poisoning attempts where attackers redirect traffic to malicious sites
-
Domains, HTTPS, and Security Certificates:
- Verify HTTPS: Verify that a website uses HTTPS (indicating encryption) and has a valid, untampered security certificate
- Sense-Checking Domain Names: Looking for subtle misspellings (e.g., “go0gle.com” instead of “google.com”) or extra words (e.g., “google-security.com”)
-
Design Flaws and Content Quality:
- Look for websites with poor grammar, misspellings, broken links, or an unprofessional design compared to the legitimate site
- Look for websites linking to content from the official website
-
Social Media Profile Scrutiny:
- Searching for duplicate profiles using the same name or brand identity
- Profile picture analysis using a reverse image search and/or AI detection
- Monitoring for reports from followers about strange messages supposedly from the account
- Looking for inconsistencies in content, posting patterns, or follower interactions
-
Monitoring System Behavior:
- Monitoring for unusual DLL loading patterns, especially the loading of system-critical DLLs from non-standard locations
-
Securing Applications (Web):
- Monitoring DNS for DNS squatting and look-alike domains for the organization-owned web applications
-
Domain Fronting:
- Monitoring network traffic for discrepancies between the Server Name Indication (SNI) field in the TLS handshake and the Host header in the subsequent HTTP requests
-
Impersonation of Trusted Processes:
- Analyze process parent-child relationships
- Verify digital signatures of executables
- Monitor network connections for unusual endpoints or protocols
- Compare service configurations against known baselines
Preventive Controls
Identity spoofing is most effective in environments where there is no supporting evidence to validate or refute the spoofed attributes being proffered. Following Zero Trust design principles of continual authentication and access control based on least privilege ensures that access to data and resources should be validated by multiple attributes, assertions, and signals.
-
Email Protection:
- Use Anti-Spoofing Tools: These include sender reputation analysis and URL/link protection to detect and block spoofed emails and to protect from phishing attacks and impersonation
- Email Origination Alerting: Add a visible header to incoming emails to alert the reader when the email originates from outside your organization and/or email domain(s)
-
Internet Protection:
- Resource Public Key Infrastructure (RPKI): A framework that uses digital certificates to verify the ownership of IP address blocks
- Route Origin Authorizations (ROAs): Cryptographically signed objects within RPKI that explicitly state which Autonomous System Number (ASN) is authorized to originate specific IP address prefixes
-
Securing Applications (Web):
- Hardening HTTP Headers: Setting X-FRAME-OPTIONS to SAMEORIGIN or DENY (or equivalent) to prevent including the applications in any malicious iFrame
-
Domain Name System (DNS) Protection:
- Secure DNS Queries: Implement DNS over HTTPS (DoH)
- Domain Name System Security Extensions (DNSSEC): Cryptographically authenticating DNS responses, ensuring their origin and integrity
-
Network/LAN Protection:
- Network Segmentation: Allows the inspection of traffic within the network at the segmentation “choke” points
- Network Intrusion and Prevention System (NIPS): Typically placed at network “choke” points allowing traffic to be analyzed in the context of the segment or the allowed flow between segments
-
Content Filtering:
- Web Content Filtering: Ideally filtering for both malicious URLs and content
- Email Content Filtering: Employing content scanning and analysis, behavioral analysis, and policy enforcement (e.g., DLP)
-
End-Point Protection:
- Endpoint Detect and Response (EDR): Providing endpoint visibility, threat detection, and analysis with both automated and manual response
- Antimalware: Providing real-time protection using signature-based and heuristic-based analysis, together with quarantine and removal
-
File Integrity Monitoring (FIM):
- Monitor critical system files and application directories for unexpected changes, including the creation or modification of DLL files
- Verify the digital signatures of DLLs before loading to ensure integrity and authenticity
-
Domain Fronting Protection:
- Implement a Secure Web Gateway (SWG): With TLS interception capacity to detect mismatches between the TLS SNI and the HTTPS host header
- Monitor and Filter Traffic: To detect anomalies in network traffic, such as mismatched domain names in the SNI and HTTPS host headers
- Collaborate with CDN Providers: To ensure measures are in place to block domain fronting and other malicious activities
- Enforce Strict Domain Policies: Implement strict policies for managing domain names and ensure that only authorized entities can make DNS or hosting changes, reducing the risk of unauthorized domain takeovers
-
Impersonation of Trusted Processes:
- Restrict users accounts to the least privileges, by allowing them only the privilege they require for their task
- Limit permission of privileged accounts so they cannot create tokens
Identity Abuse
Identity abuse occurs with the intentional misuse or exploitation of an entity’s identity attributes. This can involve a variety of harmful actions.
Overview of Identity Abuse
Threat actors will often look to abuse existing legitimate identities. This refers to the act of exploiting compromised or stolen credentials, such as passwords, tokens, or certificates, to perform malicious actions while pretending to be the legitimate owner.
More often than not, the target for abuse will be a human, as accounts linked to a person can be easily monetized. However, attacks against business and systems will look to abuse non-human identifiers and credentials.
Examples of Identity Abuse
-
Identity Theft: Assuming another person’s identity for financial gain or criminal activities
- Using stolen information to open new accounts or commit fraud
- Using stolen information to open accounts or make purchases
- Using stolen credentials to control accounts and access sensitive information
- Using a stolen identity to obtain credit or loans
- Apply for (replacement) verifiable credentials (e.g., passport, driving license, education certificates) for use in real life
-
Impersonation: Pretending to be someone else in real life or online, often to deceive or harm others
- Doxing: Accessing and publishing someone’s private information online without their consent, often with malicious intent
- Phishing: Attempting to trick someone into revealing personal information, often through fraudulent emails or websites
-
Account Takeover: Gaining unauthorized access to someone’s online accounts
- Leverage the account (often email) to reset passwords and other credentials to takeover other accounts
- Using a stolen account for social engineering
-
Synthetic Identity Fraud: Combining real (often stolen) and fake personal information to create a new, fictitious identity
- Using the synthetic identity to open new accounts or commit fraud
- Using the synthetic identity to open accounts or make purchases
- Using the synthetic identity to obtain credit or loans
-
Black Market Trade: Buying and selling stolen identity information on the dark web
- Facilitating identity theft and other criminal activities
- Stolen credentials, keys, and secrets being widely available
Real-World Examples of Identity Abuse
To put identity abuse in context, here are some real-world examples:
-
Impersonation: Andorrie Sachs had her wallet stolen by a pregnant woman who was also a regular meth user. Having Sachs’ driver’s license and other papers, she delivered her baby in Sachs’ name and abandoned her child at the hospital, leaving Sachs with a $10,000 hospital bill4
-
Personal Identifiable Information (PII) Theft and Doxing for Extortion: Mir Islam and his co-conspirators obtained PII about their victims including addresses, dates of birth, Social Security numbers, telephone numbers, email addresses, and even credit information, which they would then use to dox their victims by publicly posting this information online5
-
Password Theft for Ransomware: At a UK company, hackers gained entry to the computer system by guessing an employee’s password after which they encrypted the company’s data and locked its internal systems resulting in the company going out of business6
-
Data Breach Leading to Sale on the Dark Web: In 2013, Target’s network was breached through a third-party HVAC vendor using stolen credentials. Once inside, malware targeted the point-of-sale (POS) systems to capture credit and debit card information as customers swiped their cards, and the details were sold on the black market (dark web)7
-
Account Takeover (ATO): Over 60,000 betting accounts were compromised at DraftKings by a “credential stuffing” attack where stolen credentials (likely obtained from other data breaches) were used in the hope that users had reused their passwords, resulting in funds being drained from user accounts8
Controls Against Identity Abuse
Detective Controls
As identity abuse leverages an existing legitimate account, the primary detective controls are looking for and spotting anomalous behavior.
Behavioral and contextual analysis can indicate that a legitimate account is being used for non-legitimate purposes, thus indicating identity abuse.
Using the Zero Trust principle of logging all security events supports detecting abuse of identities, along with a feedback loop of context-based access control.
-
Unusual Activity Monitoring and User Behavior Analytics (UBA):
- Audit Trails: Maintain detailed audit trails of user activities, including login attempts, password changes, and access to sensitive information. This helps in tracing back any suspicious activities
- Access Recertification: Implement regular access recertification processes to review and validate user access permissions and ensure they are appropriate
- Configuration Monitoring: Continuously monitor the configuration of access controls and authorization mechanisms to detect any unauthorized modifications
- Log Analysis: Review and analyze security logs to identify unusual login attempts, failed authentication attempts, or other anomalies that could indicate an attack, such as logins from unusual locations, times, or devices
- Access Attempt Failures: Flag repeated failed login attempts or attempts to access sensitive systems
-
Context-Based Access Control (CBAC):
- Leverage ZT Additional Signals: Use the additional signals required for CBAC to alert if a “legitimate entity” attempts something out of context
- Account Activity: Observe unexpected transactions, password changes, or data access that doesn’t align with the legitimate user’s typical behavior
-
Email and Social Media Communication Content Analysis:
- Urgent Language/Calls to Action: Threat actors often create a sense of urgency to pressure victims into immediate action without critical thinking (e.g., “urgent action required,” “account will be suspended”)
- Requests for Sensitive Information: Legitimate organizations rarely ask for full passwords, Social Security numbers, or banking details via unsolicited emails or phone calls
- Generic Greetings: Emails starting with “Dear customer” or “To whom it may concern” instead of a personalized greeting can be suspicious
- Grammar and Spelling Errors: A common indicator is poor grammar, spelling mistakes, or unnatural sentence structure
- Unsolicited Attachments/Links: Never click on unrequested links or download unexpected attachments, even if they appear to be from a known source
Preventive Controls
Mitigation against identity abuse comes in two forms: those the organization can take, and those the entity (typically a person) can take. Both have the same aim—to prevent bad-actors from being able to steal and then misuse an identity’s persona or the attributes of that persona.
Mitigations include reducing implicit trust in the organization that supports abuse of identities, including access control based on least privilege and continual authentication.
Mitigations for Abuse
Direct Organizational-Level Mitigations
Mitigations that can be applied in any combination by an organization against the loss/theft of accounts, account information, and/or attributes include:
-
Do Not Maintain Non-Authoritative Identities: Thus, a data breach only affects attributes pertaining directly to the organization and minimizes the blast radius
-
Properly Protect Attributes: Protecting data at rest and data in transit, storing passwords and other attributes in (salted) hashes, using homomorphic encryption and/or tokenization
-
Access Recertification: Regularly recertify access requirements to ensure they remain appropriate and necessary
-
Step-Up Authentication: Requiring higher levels of certainty about the entity when the access criteria become higher risk
-
Use Short-Lived Role-Based Credentials for Application Workloads: Enable role-based authentication for workloads to replace long-term static keys with temporary, provider-issued credentials that automatically rotate
-
Implement Least Privilege Principle: Grant entities the minimum level of access necessary to perform the required function
-
Implement CBAC: Approve access requests based on context built from the signals from the participating Zero Trust pillars
-
Strong Password Policies: Where passwords are still required for authenticating entities, enforce and strengthen best practice for passwords
-
Mandate Secure Protocols: To guard against Adversary-in-the-Middle (AiTM) attacks, and enforce, where feasible, at a network level
-
Protect Account Access Abuse: With account lockout mechanisms to prevent brute-force attacks, credential stuffing prevention to detect and block repeated login attempts using known compromised credentials, and rate limiting to limit the number of login attempts per device or user account within a certain timeframe to prevent automated attacks
-
Session Management: Ensure secure session management by using unique session identifiers and implementing timeouts for inactive sessions
Indirect Organizational-Level Mitigations
Mitigations that can be taken by an organization against the misuse of a legitimate persona or attribute trying to move laterally inside a system or organization include:
-
Audit Logs: Maintain detailed logs of access and changes to authorization attributes to detect and investigate suspicious activities
-
Automated Alerts: Implement automated alerts for unusual access patterns or policy changes
-
Strong Identity Proofing Processes: To detect stolen attributes being leveraged to create new accounts or new access to systems
-
Robust Processes for Privileged Access: Implement best practices for granting, monitoring, and auditing privileged access, ideally implementing a just-in-time (JIT) access process
-
Identity Threat Detection and Response (ITDR): Monitor and analyze user activity and access management logs to detect malicious activity, and provide visibility into potential credential misuse and abuse of privileges
Entity-Level Mitigations
Mitigations that can be taken by an individual entity (usually a person) against the misuse of one of their legitimate persona or attributes include:
-
Multi-Factor Authentication (MFA): Adding an extra layer of security by requiring two or more verification methods, including but not limited to phishing-resistant MFA
-
Education and Awareness: Educate about the importance of good security practices in protecting personas and attributes
-
Biometrics for Human Entities: Enable biometric authentication where feasible and allowed by the organization
Failings in the Identity Ecosystem and How to Address Them
According to a 2024 Cisco Talos report,9 over 60% of Incident Response (IR) cases were attributed to identity-based attacks. This report also noted that in nearly 70% of ransomware cases, attackers relied on valid credentials for initial access.
This leads to a number of key areas for basic identity focus to prevent both spoofing and abuse of identities.
| Failing | Description | Potential Fixes Using Zero Trust |
|---|---|---|
| Over-Reliance on Passwords | Passwords are weak, reused, and easily compromised. | Implement passwordless authentication, enforce MFA (prefer app-based, hardware tokens, and/or phishing-resistant MFA), and use conditional access policies. |
| Inadequate Identity Lifecycle Management | Accounts often remain active after termination, leading to risks. | Automate provisioning and deprovisioning, enforce JIT access, and regularly review inactive accounts. |
| Insufficient Monitoring and Anomaly Detection | Identity-based attacks often go unnoticed due to poor monitoring. | Use ITDR tools, enable adaptive risk detection, and integrate identity logs with SIEM/SOAR platforms. |
| Lack of Role-Based Access Controls (RBAC) | Excessive or ad hoc permissions increase attack surface. | Define granular permissions for roles, enforce least privilege access, conduct regular access reviews, and detect excessive permissions. |
| Lack of Context-Based Access Controls (CBAC) | Excessive or ad hoc permissions based on roles and static signals increase attack surface. | Identify the signals to be consumed in the CBAC environment, and define the risk threshold. |
| Weak Privileged Access Management (PAM) | Unprotected admin accounts are a high-value target for attackers. | Deploy PAM solutions, enforce MFA for privileged accounts, rotate credentials, and use session auditing. |
| Limited Coverage of Non-Human Identities (Non-Person Identities) | Service accounts and API keys are often overlooked, creating vulnerabilities. | Secure non-human identities with strong authentication, lifecycle management, secrets rotation, and regular audits. Use CBAC with NHIs and monitor the usage. |
| Absence of Zero Trust Alignment | Identity management is siloed, lacking continual verification and contextual enforcement. | Enforce continual access evaluation based on context, and apply consistent policies across environments. |
| Poor Credential Hygiene Practices | Default credentials, shared accounts, and weak passwords remain prevalent. | Conduct credential audits, enforce strong password policies, use SSO and deploy tools to detect compromised credentials. |
| Enrolling Attributes for Which the Organization is Not Authoritative | Attributes quickly become stale and risk extending blast radius in the event of a breach. | Consume non-authoritative / immutable attributes from their authoritative sources, where possible in real time (consider caching if necessary) |
| Inability to Consume Assertions and Attributes from Sources the Organization Does Not Manage | Forces the enrollment of “dummy” entities in the system for which the organization is not authoritative. | Implement the ability to consume assertions and attributes from their authoritative sources. Implement systems to on-board authoritative entities (sources) |
| Inability to Validate to Third Parties for Attributes and Assertions for Which the Organization is Not Authoritative | Forces the development of workaround processes that make the synchronization of entities across unconnected systems and organizations inefficient or clumsy. | Implement the ability to provide validation of the organization’s authoritative signed attributes to third parties. |
Guiding Design and Zero Trust Principles
While the tools to both attack and protect identities and entities used in computing have become more sophisticated, the foundational elements have still stayed the same. Here, we look at the foundational elements that help prevent and minimize these risks.
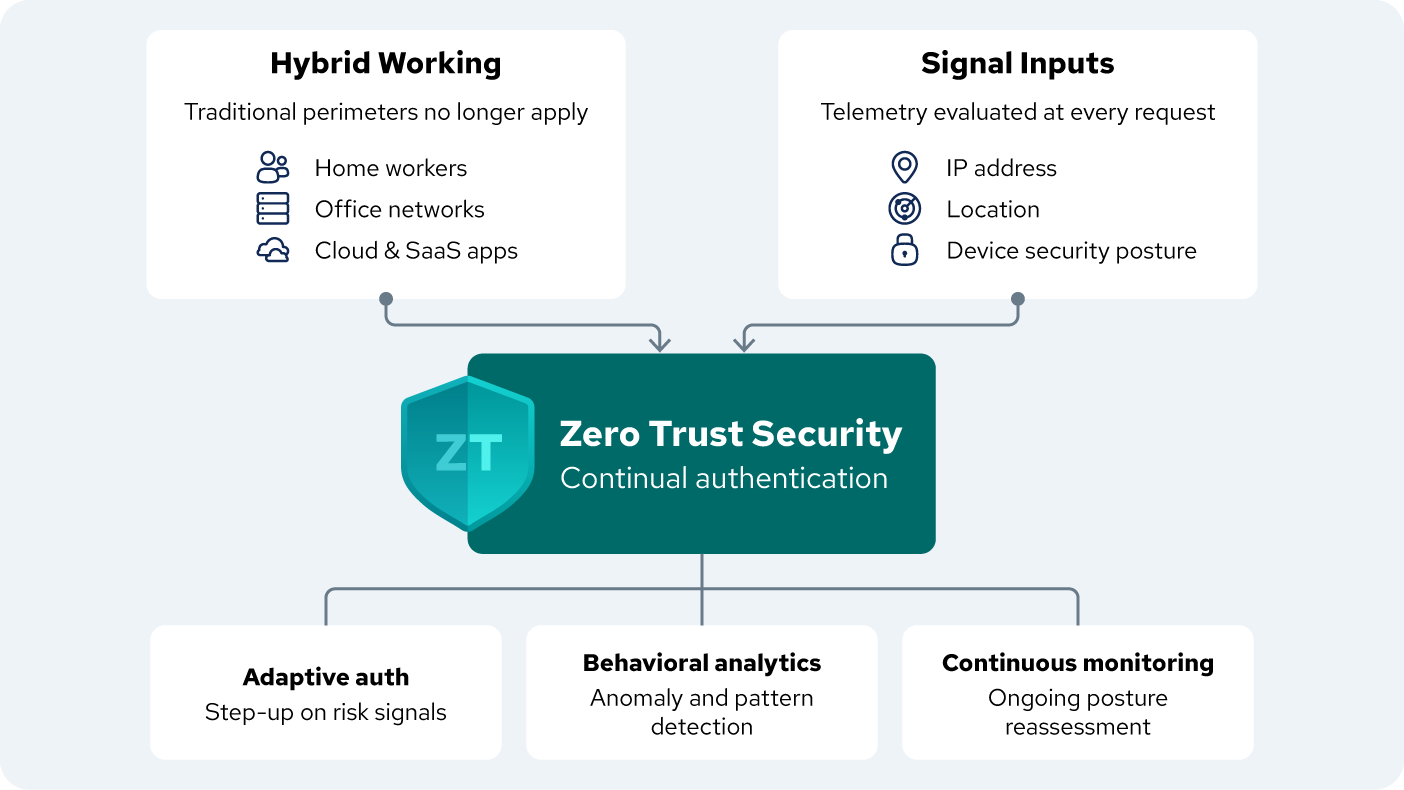
Figure 2: Zero Trust & Identity Security in a Hybrid Working World
Strategic Fundamentals
This document identifies the methods by which malicious actors can spoof and abuse identities, and these methods can be distilled into a number of key fundamental areas that we believe organizations should focus on, including following Zero Trust principles (in addition to improving current identity management practices) to better protect themselves in the future.
-
Context-Based Access Control (CBAC): Particularly in a Zero Trust environment where access to data, systems, and devices are granted based on the attributes proffered by the entity, in conjunction with signals that support that access request
-
Access Requests Should be Risk-Based: The reliance on binary authentication, authorization, and access should be eliminated. Instead, move to a risk-based approach where access requests are assessed in real-time based on all the attributes and signals available together with the access being requested
-
Attributes Proffered Should be Validated by Their Authoritative Source: Most information, particularly about people, has been breached or can be socially engineered. The challenge is where a third party can know a person’s information but are unable to spoof being that person!
-
Understand the Level of Immutability: When evaluating an attribute, it is key to determine the probability that the attribute actually refers to the entity proffering it (or even whether the agent that is proffering on behalf of the entity has been granted “agency”). Understanding just how closely linked the entity and the assertion are is essential
-
Do Not Maintain Non-Authoritative Identities (Persona and Attributes): Instead, consume them from their authoritative source, caching them if necessary for a time commensurate with your risk tolerance
-
Treat Human and Non-Human Identities (NHI’s) as Identical: Understand the authoritative sources for all attributes being proffered by entities and ensure that your contextual management access system is able to consume them and analyze them to make a risk-based decision about access (See Appendix A)
Cost of Identity Spoofing and Abuse
Costs of identity spoofing and abuse in the IT landscape are continuously growing. Financial and non-financial impacts are multi-faceted and can be devastating. Direct and indirect costs may occur.
Examples of direct financial costs include:
-
Average Cost of a Data Breach: The global cost of a data breach is a key metric. As of 2024, the average cost of a data breach is $4.88 million USD.10 In the US, the cost is significantly higher, reaching over $9 million USD per incident. This cost is impacted by many factors including the related industry (e.g., healthcare breaches are often the most expensive), the type of data stolen (PII is the most costly), and the duration of the breach
-
Post-Incident Clean-Up: Activities after an incident are a significant portion of the costs. These include:
- Legal Fees and Fines: A complex web of legal requirements, from lawsuits by affected individuals to fines from regulatory bodies like the Federal Trade Commission (FTC) or the General Data Protection Regulation (GDPR)
- Ransom Payments: In cases of ransomware attacks, organizations may pay high costs to cybercriminals in order to recover their data, though this is not a guarantee of data recovery, and it is not a recommended practice
- Forensic Investigation: Costs for hiring security experts to determine the cause, scope, and duration of the breach
-
Business Lost and Operational Downtime: Depending on its magnitude, a breach can decrease business operations, leading to productivity and revenue loss
Indirect costs are often more insidious and long-lasting than the direct financial hit. They include:
-
Reputational Damage and Loss of Customer Trust: Data breaches are often considered a public failure of a company’s duty to protect its customers, which can lead to severe loss of trust[^13]
-
Increased Insurance Premiums: Insurance premiums will certainly increase, adding long term operational costs
-
Loss of Intellectual Property: In some attacks, the goal is to exfiltrate valuable intellectual property, such as trade secrets, business strategy, or product design details. A company can lose their competitive advantages in the market when compared to similar organizations
Future Considerations
Artificial intelligence (AI) and machine learning (ML) can be used to generate realistic and convincing fake or altered content, such as images, videos, audio, or text, that can be used for spoofing or impersonation. For example, deepfake technology can create synthetic face or voice samples that can fool biometric or human verification systems.
This implies that there is a need to be able to check the provenance of an image, email, voice call, video call, request from a system, an AI agent or system claiming agency, and so on against the authoritative source (that we trust) for that entity.
Conclusion
The threat actors behind spoofing and abusing identities are skilled, diverse, and motivated by different objectives, such as financial gain, espionage, sabotage, or activism. However, spoofing and abusing identities can also be performed by less skilled or opportunistic attackers who may use readily available tools or services to launch their attacks.
The methods that are most often used by threat actors to spoof and/or abuse identities are constantly evolving and becoming more advanced, as they try to evade detection and countermeasures. Some of the methods that are currently used or emerging include:
-
Cryptographic Algorithms and Protocols: These technologies can be used to encrypt or obfuscate the communication or data that is used for spoofing or abusing identities, making it harder to trace or analyze. For example, encryption can hide the true content or origin of an email or a packet, while protocols such as Tor or VPN can mask the real IP address of the sender or the receiver
-
Botnets and Proxies: These technologies can be used to amplify or diversify the spoofing or abuse of identity attacks by using multiple compromised or rented devices or servers to send or relay the malicious traffic or requests. For example, botnets can launch distributed denial-of-service (DDoS) attacks using spoofed IP addresses, while proxies can hide the true location or identity of the attacker
-
Social Engineering: Tricks a user of a social media platform, email system, phone system, and so on into revealing information to an entity they believe is known or friendly
-
Malicious Use of AI: The increasing use of AI to acquire attributes, steal identities, create identities, and use identities fraudulently
Companies face significant challenges and risks from the spoofing and/or abuse of identities, as they can result in data breaches, financial losses, reputational damage, legal liabilities, or operational disruptions. Therefore, companies need to adopt a comprehensive and proactive approach to protect against these and future threats, by implementing various measures:
-
Security Awareness and Education: This involves training and informing employees and customers about the common signs and methods of spoofing and abuse of identities, and how to avoid or report events. For example, employees and customers should be taught how to verify the authenticity and legitimacy of an email, a call, or a website, and how to use strong and unique passwords or MFA
-
Security Policies and Procedures: This involves establishing and enforcing clear and consistent rules and guidelines for the use and management of the systems, data, and accounts that are targeted when spoofing and abuse of identities occurs. For example, policies and procedures should define the roles and responsibilities of the users and the administrators, the access rights and privileges of the users and the devices, and the security standards and best practices for the systems and the data
-
Security Technologies and Solutions: This involves deploying and updating various tools and systems that can detect, prevent, or mitigate attacks or that can enhance the security and resilience of the systems, data, and accounts. For example, antivirus, firewall, spam filter, email authentication, network monitoring, intrusion detection and prevention, encryption, digital signature, biometric verification, backup, and recovery. Aligning architectural patterns, particularly designs based on Zero Trust, with a modern approach to granting entitlement for access to those systems is critical for ensuring solutions are risk-based and leverage signals and attributes from all the entities in the transaction chain
Glossary
The terms used in this document come from a variety of sources (some contradictory, as is common in this field) and are provided here for clarity.
-
Attribute: A quality or characteristic ascribed to someone or something ([NIST SP 800-63-4, Digital Identity Guidelines CSRC](https://csrc.nist.gov/pubs/sp/800/63/4/final)). An attribute or set of attributes that uniquely describe a subject within a given context (Identity and Access Management (IAM) Glossary, CSA and 10 Essential Identity and Access Management (IAM) Terms, CSA) -
Assertion: An assertion made about a subject. Used interchangeably with “claim.” Assertions contain attributes, which are the specific pieces of information being claimed (Verifiable Credentials Data Model v2.0, W3C)
-
Entity: An individual (person), organization, device, or process. Used interchangeably with “party” (FIPS 186-5 - NIST Technical Series Publications). Anything that can be referenced in statements as an abstract or concrete noun (Verifiable Credentials Data Model v2.0, W3C)
-
Identifier: A data object that is associated with a single, unique entity (e.g., individual, device, session) within a given context and is never assigned to any other entity within that context (NIST SP 800-63-4, Digital Identity Guidelines, CSRC)
-
Identity: The philosophical definition of identity. In metaphysics, identity (from Latin: identitas, meaning “sameness”) is the relation each thing bears only to itself. Identity/sameness is therefore, viewed from the perspective of the entity, a complete set of attributes grouped into logical personas (Noonan, H. and Curtis, B., “Identity”, The Stanford Encyclopedia of Philosophy (Fall 2022 Edition), Edward N. Zalta & Uri Nodelman (eds.), and Audi, R. (1999). “Identity”, The Cambridge Dictionary of Philosophy. Cambridge University Press.)
-
Persona: In Jungian psychology, the persona is the public personality that is presented to the world. A model of an individual’s public personality based on data and maintained by transactions, and intended for use as a proxy for the individual. Often referred to from the perspective of the relying party as “digital identity.” A set of attributes that uniquely describes an entity within a given context (Clarke, R. (1994, June). The Digital Persona and its Application to Data Surveillance. The Information Society, 10(2), 77-92.)
- Trust: The confidence or belief one entity holds about the integrity, ability, or character of another (Facets of Trustworthiness in Digital Identity Systems, The Alan Turing Institute)
Appendix A: Entities
An entity (and entity type) is a unique “thing” with distinct and independent existence. Any entity type may interact with any other (in that way, they are functionally identical) and the interaction creates a persona that gives context.[^14]
Examples of Human and Non-Human Entities
This is a non-exhaustive list of entity types and their identities used in modern computing to provide context for this paper.
-
People:
- Humans
-
Devices (Machine Identities):
- Computers
- Phones
- Internet of Things (IoT)
- Vehicles
- Printers
- Personal Video Recorders (PVRs)
- Bring Your Own Device (BYOD)
-
Organizations:
- Legal Organizations
- Families
- Organization Groupings
-
Code:
- Code
- Executable Programs
- Self-Protecting Code
- Digital Rights Management (DRM)
- Signed Code
-
Agents (and Entities to Which One Entity Grants Agency):
- Human Agents
- Delegations
- AI Programs
- Bots/Scripts (Software agents or automated processes)
- Robotic Process Automation (RPA) Bots (Bots that mimic human actions)
- Machine Learning Models
-
Other:
- Workloads/Service Accounts/System Accounts
- API Tokens/Keys
- Virtual Machines (VMs)
- Containers/Pods (e.g., Kubernetes)
- Cloud-Based Scripts (DevOps workflows for automated deployments, system configurations, and resource scaling)
- Application-to-Application (A2A) (Identities that facilitate communication and data exchange between software applications)
Appendix B: Threat Modeling Identity-Based Attacks
Threat modeling is the process of using hypothetical scenarios, system diagrams, and testing to help secure systems and data with many threat modeling frameworks available, such as STRIDE, PASTA, DREAD, MITRE ATT\&CK, and OWASP Top Ten.
Based on threat modeling output, risk analysis and evaluation can be performed and countermeasures and strategies put in place to mitigate those risks.
STRIDE Method
The Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Escalation of Privileges (STRIDE) method helps to categorize and understand potential threats by breaking them down into six key types:
- Spoofing: Impersonation of a legitimate user or system (e.g., phishing for credentials)
- Tampering: Unauthorized modification of identity data or attributes (e.g., altering user roles)
- Repudiation: Denial of an action or event by a user (e.g., claiming not to have performed a transaction)
- Information Disclosure: Unauthorized access to sensitive identity information (e.g., data breaches of user databases)
- Denial of Service: Preventing legitimate users from accessing identity services (e.g., locking out accounts through repeated failed login attempts)
- Elevation of Privilege: Unauthorized granting of higher access rights (e.g., exploiting vulnerabilities to gain administrator access)
PASTA Model
The Process for Attack Simulation and Threat Analysis (PASTA) model provides a structured, seven-step methodology to understand and mitigate risks. It begins by defining the business and security objectives related to identity, followed by a detailed breakdown of the application architecture and its interaction with identity systems.
Subsequently, threat enumeration and deep-dive analysis are conducted, identifying potential identity-based attack vectors such as phishing, credential stuffing, insider threats, or abuse of privileged access.
Vulnerability analysis then uncovers weaknesses in identity management systems, authentication protocols, or authorization mechanisms. The model then moves to attack simulation, where identified threats are tested against the system to understand their potential impact.
Finally, risk and impact analysis quantifies the potential damage of successful identity attacks, leading to the formulation of an effective strategy for managing and mitigating these specific risks, focusing on controls like multi-factor authentication, robust access control, and continuous identity monitoring.
DREAD Model
The Damage, Reproducibility, Exploitability, Affected Users, and Discoverability (DREAD) model provides a structured approach to assessing the severity of potential threats by considering five key factors:
- Damage: Quantifies the impact of a compromised identity, such as financial loss, reputational harm, or unauthorized access to sensitive data
- Reproducibility: Assesses how easily an attacker can consistently replicate the identity attack, like repeatedly bypassing multi-factor authentication
- Exploitability: Measures the effort and resources required for an attacker to successfully execute the identity attack, such as exploiting a vulnerability in an authentication system
- Affected Users: Determines the number or criticality of users whose identities could be compromised, ranging from a single individual to an entire organization’s user base
- Discoverability: Evaluates how easily an attacker can identify the weakness or vulnerability in the identity system that could lead to an attack, like finding an exposed API key or misconfigured identity provider
MITRE ATT\&CK Model
The MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT\&CK) model provides a comprehensive knowledge base of adversary tactics and techniques based on real-world observations, and its application to identity attacks offers a structured approach to threat modeling.
Within the ATT\&CK model, various tactics such as Credential Access, Discovery, and Persistence are particularly relevant to identity-centric threats. For instance, an adversary might employ techniques like Brute Force or Password Spraying under Credential Access to obtain legitimate user credentials. Subsequently, they could use Account Discovery or Group Policy Discovery under Discovery to identify high-value accounts or vulnerable configurations. Finally, techniques like Valid Accounts or Modify Authentication Process could be used under Persistence to maintain unauthorized access.
By mapping observed or anticipated identity attack behaviors to these specific ATT\&CK tactics and techniques, organizations can effectively identify potential vulnerabilities, understand adversary methodologies, and prioritize defensive countermeasures to protect their identity infrastructure.
The OWASP Top Ten Model
The OWASP Top Ten model provides a framework for understanding and mitigating identity-related threats within a threat modeling context. When applying this model, developers and security professionals can specifically analyze how each of the 10 categories—such as Broken Access Control, Injection, Security Misconfiguration, and Identification and Authentication Failure—can manifest in identity attacks.
For instance, Broken Access Control directly relates to unauthorized privilege escalation through identity manipulation, while Identification and Authentication Failures explicitly addresses weak credential management, session hijacking, or flawed multi-factor authentication, all of which are primary vectors for identity compromise.
Appendix C: Additional Resources
-
[Identity Awareness, Protection, and Management Guide ODNI](https://www.odni.gov/files/NCSC/documents/campaign/DoD_IAPM_Guide_March_2021.pdf) -
[Microsoft says DOD needs to be better at detecting synthetic identities. And do it sooner Biometric Update](https://www.biometricupdate.com/202205/microsoft-tells-dod-it-needs-to-be-a-leader-in-detecting-synthetic-identities) -
[Non-Person Entity (NPE) - Glossary CSRC](https://csrc.nist.gov/glossary/term/non_person_entity) -
[Special Publication 800-63A, Digital Identity Guidelines NIST](https://pages.nist.gov/800-63-4/sp800-63a.html) -
[Synthetic Identity Payments Fraud FedPayments Improvements](https://fedpaymentsimprovement.org/wp-content/uploads/synthetic-identity-fraud.pdf) -
[Synthetic Identities: The Darker Side Of Generative AI Forbes](https://www.forbes.com/sites/forbestechcouncil/2024/05/29/synthetic-identities-the-darker-side-of-generative-ai/)
| [^2]: [Watch out for this triple-pronged PayPal phishing and fraud scam | ZDNET](https://www.zdnet.com/article/watch-out-for-this-triple-pronged-paypal-phishing-and-fraud-scam/) |
| [^3]: [AI scam calls: This mom believes fake kidnappers cloned her daughter’s voice | CNN](https://edition.cnn.com/2023/04/29/us/ai-scam-calls-kidnapping-cec/index.html) |
| [^13]: [Impact of Identity Theft on Businesses in 2023 | LoginRadius](https://www.loginradius.com/blog/identity/identity-theft-impact-on-businesses-in-2023) |
| [^14]: [Identity 3.0 Definitions | The Global Identity Foundation](https://www.globalidentityfoundation.org/downloads/Identity_30_Definitions.pdf) |
-
How this scammer used phishing emails to steal over $100 million from Google and Facebook ↩
-
Texas toll tag users targeted by ‘smishing’ scam, TxDOT warns ↩
-
5 peculiar cases of identity theft and how they could have been prevented - Innovatrics ↩
-
New York Man Sentenced To 24 Months in Prison For Internet Offenses, Including “Doxing,” “Swatting,” Making a False Bomb Threat, and Cyber-Stalking ↩
-
Weak password allowed hackers to sink a 158-year-old company - BBC News ↩




