The Four Pillars of CASB: Visibility
Published 12/04/2019
By Juan Lugo Product Marketing Manager at Bitglass
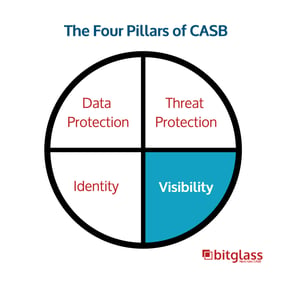
Due to the potential for data leakage in the cloud, the use of CASBs (cloud access security brokers) is needed in order to maintain visibility over data that has gone beyond the reach of on-premises tools.
Activity Logs
When it comes to sensitive data, an organization must have full visibility and knowledge over how it is being used. CASBs provide detailed logs on all cloud transactions, so any logins, uploads, or downloads are always recorded. App-specific behaviors such as external file sharing are also logged, helping organizations know the whereabouts of data if it is shared. These logs also allow IT teams to filter through them in order to gain more visibility into the activity within the enterprise.
Shadow IT
Shadow IT, also known as unsanctioned applications, are classified according to risk – allowing organizations to decide what needs to be blocked. Some more traditional CASBs focus their resources on manually detecting and cataloging unsanctioned cloud applications. This is typically done through teams of people who scour the internet to reactively evaluate applications as they arise or are updated. Other CASBs focus on creating a system that automatically detects, scrutinizes, and classifies any application. This automated system, referred to as Zero-day Shadow IT Discovery, uses a machine learning approach to evaluate apps on the fly.
CSPM
In addition to the above, cloud security posture management (CSPM) detects misconfigurations for infrastructure as a service (IaaS) platforms, which often require extensive configurations in order to make sure that they function properly. Having a strong cloud security posture on these platforms is a critical step to prevent data leakage. Storage solutions, like AWS for instance, have to be configured properly or it can result in sensitive data becoming publicly accessible. This is precisely what happened in the Capital One breach.
Organizations utilizing CSPM enable themselves to identify and remediate any misconfigurations. To learn about cloud access security brokers (CASBs) you can download the Top CASB Use Cases.
This blog is part of a series, read the other blog posts here
Unlock Cloud Security Insights
Subscribe to our newsletter for the latest expert trends and updates
Related Articles:
When is SD-WAN Zero Trust and When is it Not?
Published: 03/08/2023
What is a CASB and How Does it Integrate with DLP?
Published: 12/19/2022
Security Service Edge (SSE) Reflects a Changing Market: What You Need to Know
Published: 02/24/2022
Multi Cloud Security
Published: 02/17/2022





-reflects-a-changing-market-what-you-need-to-know.jpg)
