FinCloud Security
Improving the security of global cloud adoption for the financial services industry.
The Financial Services Industry (FSI) adoption of cloud computing services has grown extensively in recent years. This trend is expected to continue with the migration of business applications to the cloud, driven both by increasing maturity, sophistication and resilience of cloud-native services and the declining availability of COTS software for on premises use. This includes both traditional and new and innovative technology for banking, commerce, financial transactions, and the exchange of financial and economic data.
CSA's FinCloud Security engages current industry leaders and includes a Leadership Committee to help identify the topics of most interest to the industry. CSA will develop, assemble and share valuable resources such as use cases, research materials, webinars, education, analyst briefings, assurance frameworks, and extensions of the CCM or STAR program. CSA will also organize and host virtual and in person events with significant financial sector content. If you're interested in learning more, you can email us at [email protected].
Latest News from the Financial Services Industry
.jpg)

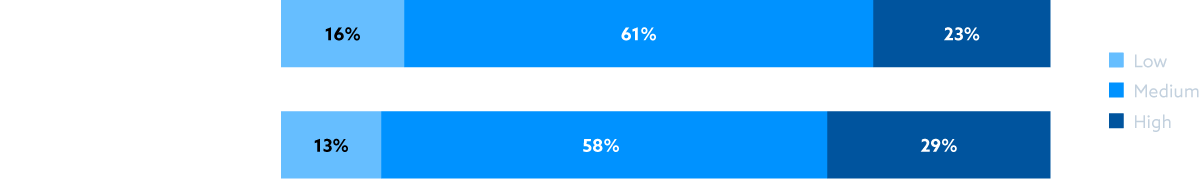
Identifying Gaps
How Knowledgable are organizations regarding:
Opportunities in Financial Services

Zero Trust safeguards financial clouds, preserving data integrity.

IoT and edge computing amplifies the complexity of security and privacy.

Blockchain protects sensitive data, transactions, and meets compliance.
Artificial Intelligence requires data care, transparency, ethical considerations.
Quantum computing adds urgency to prepare for future threats.
FinCloud Security Initiatives
Learn from the Experts
FinCloud Fridays
A monthly webinar series about the financial industry's unique challenges in cloud.
Upcoming and past webinarsFinancial Service Industry Briefings
An industry expert gives a topic-specific presentation. This initiative is only available to CSA members.
Learn about CSA membershipExplore FinCloud Resources
HSM as a Service
An upcoming white paper describing the Hardware Security Module as a Service cloud delivery model for key management and cryptographic operations.
View the Key Management Working GroupMapping to PCI DSS v4
Mapping of the CCM v4 to the latest version of the PCI DSS v4.
Access the mapping and learn moreFinancial Service Addendum to the CCM:
A framework for the financial sector toward a secure adoption of cloud services, and to limit the challenge of compliance fatigue for both CSPs and Financial Institutions.
View the CCM Working GroupJoin the Conversation
Financial Services Industry Community on Circle
Circle is a platform space for you to connect, collaborate and share knowledge with like-minded professionals from around the world. You will have access to the latest industry trends, best practices, and emerging threats related to the Financial Services Industry.
On Circle, you can access exclusive resources, participate in events, and engage in discussion on the topic of financial services. Whether you are looking to expand your knowledge, build your professional network, or stay on top of the latest trends, this CSA community platform is an essential resource.
Leadership Committee
CSA looks to our Leadership Committee to contribute to and advise on the overall strategy and roadmap of FinCloud Security. This committee is made up of participants in security leadership roles within financial institutions, the payment ecosystem (including cryptocurrency), and other organizations that initiate or manage financial data and assets within cloud environments.
This committee is reserved for the participation of individuals who work for an organization that is recognized as a CSA corporate member. Learn more about corporate membership here.

Stefani Alger
SWIFT
This person does not have a biography listed with CSA.

Imre Bako
Commerzbank
This person does not have a biography listed with CSA.

James Barber
GlobalPay
This person does not have a biography listed with CSA.

Rolf Becker
Co-Founder and Chair at UBS
Rolf A. Becker is Head Service Control Governance at UBS, globally responsible for Cloud Governance regarding Risk and Control over the UBS Group Cloud adoption and for outsourcing to external cloud-based 3rd party services. Previous roles have been the management of the Cyber and Information Security Portfolio reporting to the UBS CISO at a global level, and the management of the Client Data Confidentiality Program Unstructured Data Protec...

Fred Budd
Vice President, Information Security Engineering, Mastercard
Fred Budd is serving as Vice President, Cloud Security for Mastercard. In this role, he is responsible for the protection of Mastercard’s cloud platforms and driving the evolution of security practices. Fred has over 20 years of diverse experience in security architecture, technology strategy and governance, privacy and compliance, identity management, telecommunications, IT operations, and product innovation. In the past decade, he has foc...

Alicia Cade
GCP
This person does not have a biography listed with CSA.

David Cross
Oracle
This person does not have a biography listed with CSA.

Tom Deprins
Azure
This person does not have a biography listed with CSA.

Jason DeVoe
Voya
This person does not have a biography listed with CSA.

Thomas Dirk
Commerzbank
This person does not have a biography listed with CSA.

Aly Farooqui
IBM
This person does not have a biography listed with CSA.

Jez Goldstone
Director of Security Architecture, Cloud & Innovation, Barclay Card
This person does not have a biography listed with CSA.

Christian A. Gorke
Commerzbank
This person does not have a biography listed with CSA.

Sean Gray
Chase
Security Strategy, Threat Management. Senior Director, Information Security Strategy and Threat Mgmt at PayPal.

Jonathan Gutierrez
Mastercard
This person does not have a biography listed with CSA.

Stacy Hughes
Voya
This person does not have a biography listed with CSA.

Bill Izzo
Director, Cloud Security Governance at Depository Trust and Clearing Corporation
Innovative leader with a strong technical and business background with a track record of success across multiple technology domains and markets. Senior business management and technical leadership experience in the DOD, Private, and Government sectors. Years of experience in the management of medium to large network and systems engineering teams with significant experience in the management of large multi-million dollar data com...

Phoebe Kao
Azure
This person does not have a biography listed with CSA.

Shaun Khalfman
Discover
This person does not have a biography listed with CSA.

David Kliemann
IBM
This person does not have a biography listed with CSA.

Sunil Malik
Discover
This person does not have a biography listed with CSA.

Cheri McGuire
Chief Technology Officer, SWIFT
Ms. McGuire is a technology and cyber security leader with over 30 years in strategy, policy, operations and risk, and spanning the financial, IT, consulting and government sectors. She currently serves as the Chief Technology Officer at SWIFT, a member-owned cooperative providing secure financial messaging services and products that connect more than 11,000 financial organizations globally. In her role as CTO, she has responsibility for th...

David Nickles
AWS
David Nickles is a Global Audit Program Manager for FSI’s at Amazon Web Services (AWS). His work focuses on enabling financial services institutions to move their workloads to the cloud by providing sound guidance for building programs to ensure regulatory, governance, risk, compliance, audit, and security control requirements are met, align to industry best practices, and appropriate due diligence activity is completed. Prior to AWS, David...

Sofia Pogrebynska
Paypal
This person does not have a biography listed with CSA.

Ronald Ritchey
Barclay Card
This person does not have a biography listed with CSA.

Stephan Scharf
BlackRock
This person does not have a biography listed with CSA.

Nashira Spencer
DTCC
This person does not have a biography listed with CSA.

David Stone
Google (GCP)
This person does not have a biography listed with CSA.

Erika Voss
Capitol One
This person does not have a biography listed with CSA.

James Wilkins
UBS
This person does not have a biography listed with CSA.
Related Resources
View additional resources related to the advancements in the technology of financial services.
State of Financial Services in Cloud
Cloud Octagon Model
Blockchain DLT Use Cases







