This localized version of this publication was produced from the original source material through the efforts of chapters and volunteers but the translated content falls outside of the CSA Research Lifecycle. For any questions and feedback, contact [email protected].
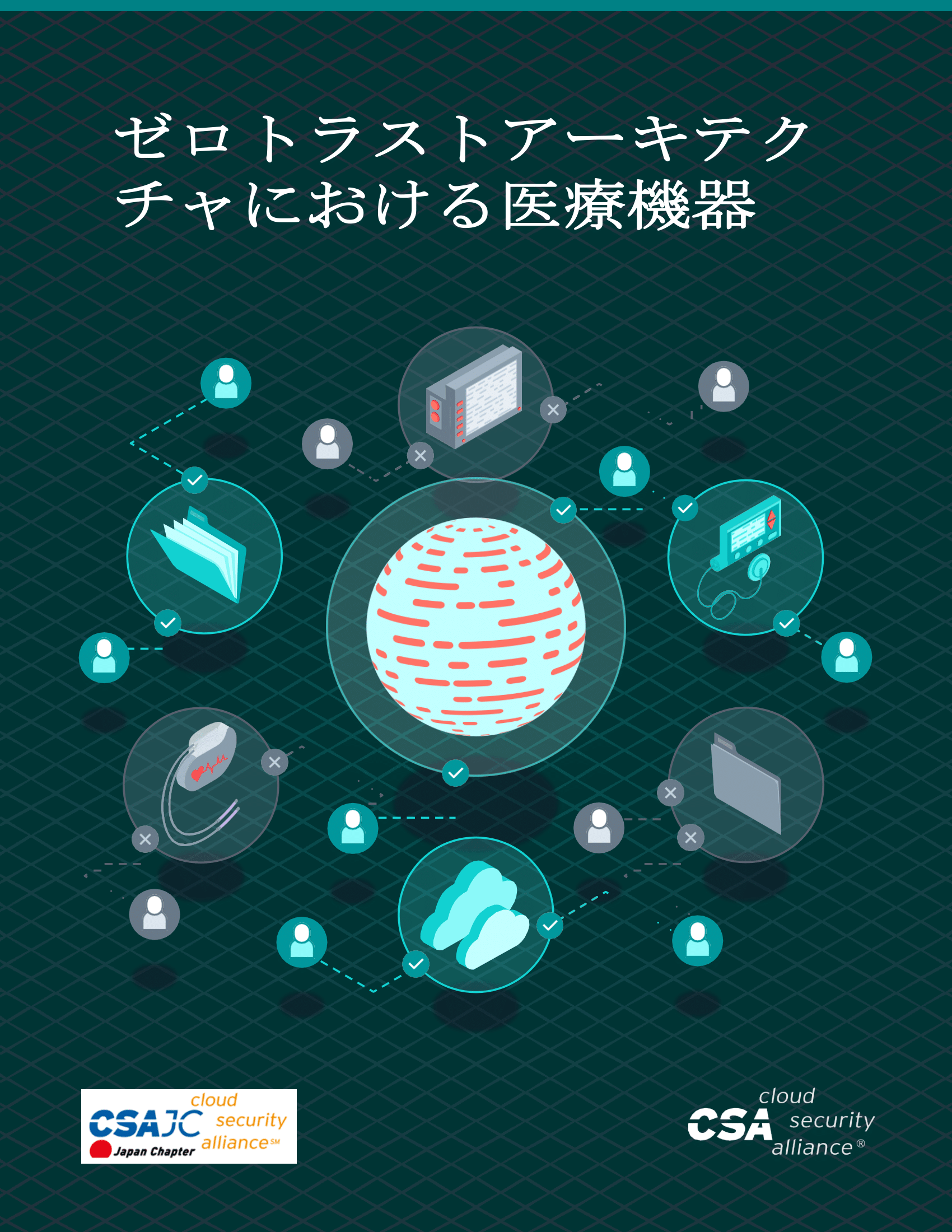
Today’s medical devices often connect to the cloud, which increases the risk by expanding the attack surface. This presents the Healthcare Delivery Organizations (HDOs) with threats and vulnerabilities, technology issues, software risks, and human factors. As a result, security architects are forced to re-examine the concept of identity. Essentially, every connected medical device has an identity and must be under consideration within the Zero Trust Framework.
Today’s medical devices often connect to the cloud, which increases the risk by expanding the attack surface. This presents the Healthcare Delivery Organizations (HDOs) with threats and vulnerabilities, technology issues, software risks, and human factors. As a result, security architects are forced to re-examine the concept of identity. Essentially, every connected medical device has an identity and must be under consideration within the Zero Trust Framework.
Download this Resource
Prefer to access this resource without an account? Download it now.