KeePass CVE-2023-32784: Detection of Processes Memory Dump
Published 07/20/2023
Originally published by Sysdig.
Written by Miguel Hernández.
During May, a new vulnerability CVE-2023-32784 was discovered that affected KeePass. KeePass is a popular open source password manager which runs on Windows, Mac, or Linux. The vulnerability allows the extraction of the master key in cleartext from the memory of the process that was running. The master key will allow an attacker to access all the stored credentials.
We strongly recommend updating to KeePass 2.54 to fix the vulnerability.
In this article we explain the new vulnerability CVE-2023-32784, how it works, and how to detect this type of attack when the attacker gains full access to your system and performs advanced techniques to steal your credentials.
Credentials in Memory Linux
When we talk about credentials in Linux, we usually think of the /etc/shadow file, but that is not the only place where passwords can be stored. Many processes also store credentials in memory, which malicious tools will try to extract. For example, the proc directory described below is a popular vector for this type of attack.
From the Linux Kernel Doc:
“The directory /proc contains (among other things) one subdirectory for each process running on the system, which is named after the process ID (PID).”
MITRE defined that the adversaries may gather credentials from the proc filesystem as OS Credential Dumping: Proc Filesystem T1003.007.
What is KeePass CVE-2023-32784?
CVE-2023-32784 allows the recovery of the cleartext master password from a memory dump. The memory dump can be a KeePass process dump, swap file (pagefile.sys), hibernation file (hiberfil.sys), or RAM dump of the entire system.
KeePass 2.X uses a custom-developed text box for password entry, SecureTextBoxEx. The flaw exploited in this CVE is that for every character typed, a leftover string is created in memory. Because of how .NET works, it is nearly impossible to get rid of it once it gets created. For example, when “Password” is typed, it will result in these leftover strings: •a, ••s, •••s, ••••w, •••••o, ••••••r, •••••••d. The first character cannot be recovered.
To reproduce the scenario, we use a 18.04.1-Ubuntu with the KeePass 2.38 version for Linux. The Proof of Concept (PoC) is based on this Github repository that also is part of the original PoC.
The PoC we use follows the steps below to extract the KeePass secret key:
- First, scan all
/proc/<pid>/cmdlinefiles and store the pid of ones with the keyword KeePass. - Then, acquire the addresses of memory maps in
/proc/<pid>/mapsthat aren’t directly associated with a library. - Finally, store the memory of all those maps into a buffer by taking advantage of
/proc/<pid>/mem. Parse the memory to try and find leftover strings from when the user typed their master password, strings that look like •a, ••s, •••s, in sequence.
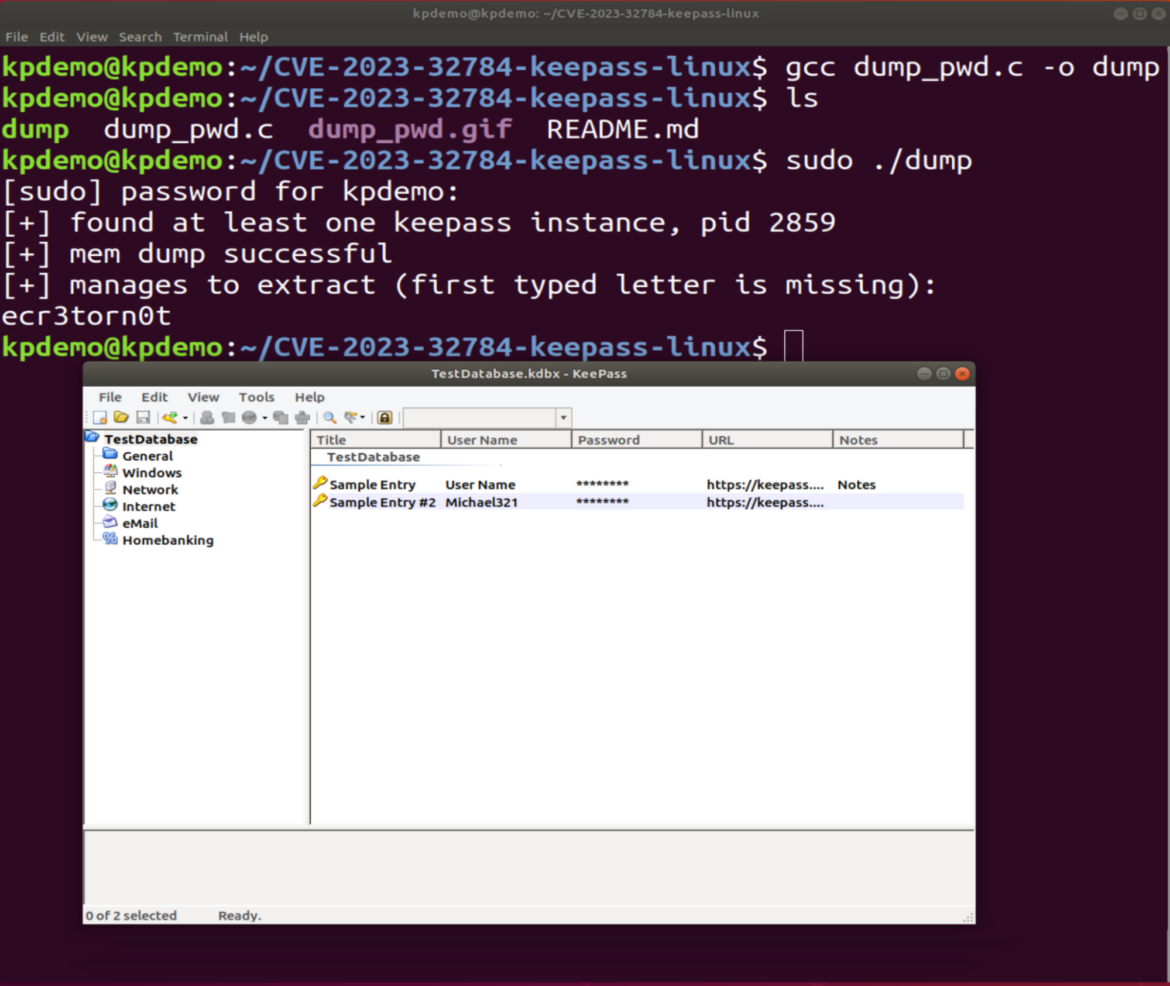
As we can see in the image above, the master key is exposed without the first character.
How to Detect KeePass CVE-2023-32784
To detect this type of attack, we should be able to monitor access to the /proc folder by an unknown process. This will trigger an alert and we can investigate further.
In this scenario, we need to adjust the rule Read environment variable from /proc files or create a new one.
To correctly trigger this rule, we should modify the condition to catch the read of /proc/<pid>/cmdline, /proc/<pid>/maps, or /proc/<pid>/mem, which is used in the PoC to obtain the KeePass master password.
- rule: Dump memory detection
desc: An attempt to read process environment variables from /proc files
condition: >
open_read and container and (fd.name glob "/proc/*/mem" or fd.name glob "/proc/*/maps")
output: >
Detected process memory dump to search for credentials (proc.name=%proc.name
proc.pname=%proc.pname fd.name=%fd.name container=%container.info evt.type=%evt.type
evt.arg.request=%evt.arg.request proc.pid=%proc.pid proc.cwd=%proc.cwd proc.ppid=%proc.ppid
proc.cmdline=%proc.cmdline proc.pcmdline=%proc.pcmdline)<small>
<span class="shcb-language__paren"></span></small>With this new rule, we are able to detect the exploitation of CVE-2023-32784.
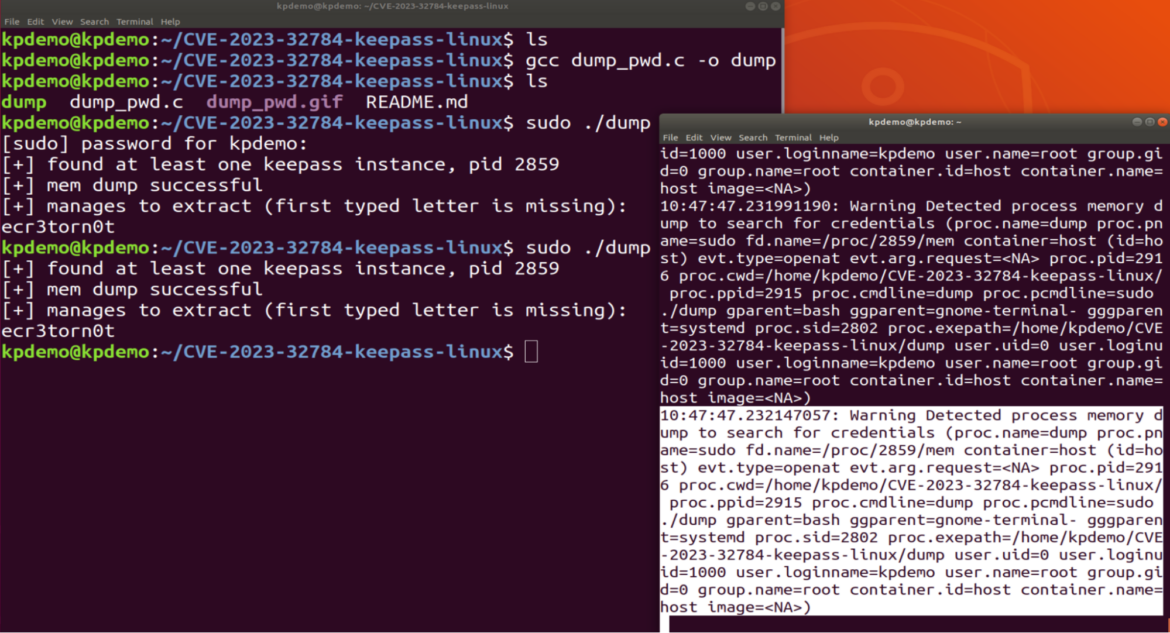
The alert contains all the information we needed to continue investigating the threat.
10:47:47.232147057: Warning Detected process memory dump to search for credentials (proc.name=dump proc.pname=sudo fd.name=/proc/2859/mem container=host (id=host) evt.type=openat evt.arg.request=<NA> proc.pid=2916 proc.cwd=/home/kpdemo/CVE-2023-32784-keepass-linux/ proc.ppid=2915 proc.cmdline=dump proc.pcmdline=sudo ./dump gparent=bash ggparent=gnome-terminal- gggparent=systemd proc.sid=2802 proc.exepath=/home/kpdemo/CVE-2023-32784-keepass-linux/dump user.uid=0 user.loginuid=1000 user.loginname=kpdemo user.name=root group.gid=0 group.name=root container.id=host container.name=host image=<NA>)<small> <span class="shcb-language__paren"></span></small>
As mentioned in the exploit, if the attacker has sufficient permissions and capabilities within your machine, the attacker may be able to perform any malicious action. However, this rule can give us an indication of whether our credentials have been breached and act accordingly.
More Tools to Dump Process Memory
If we research a little more about this type of technique, we see that there are other tools that perform a similar action. Let’s see a couple and how to detect them in the same way.
Mimipenguin
Mimipenguin 2.0 is a tool to dump the login password from the current Linux desktop user. It is adapted from the idea behind the popular Windows credential stealing tool mimikatz.
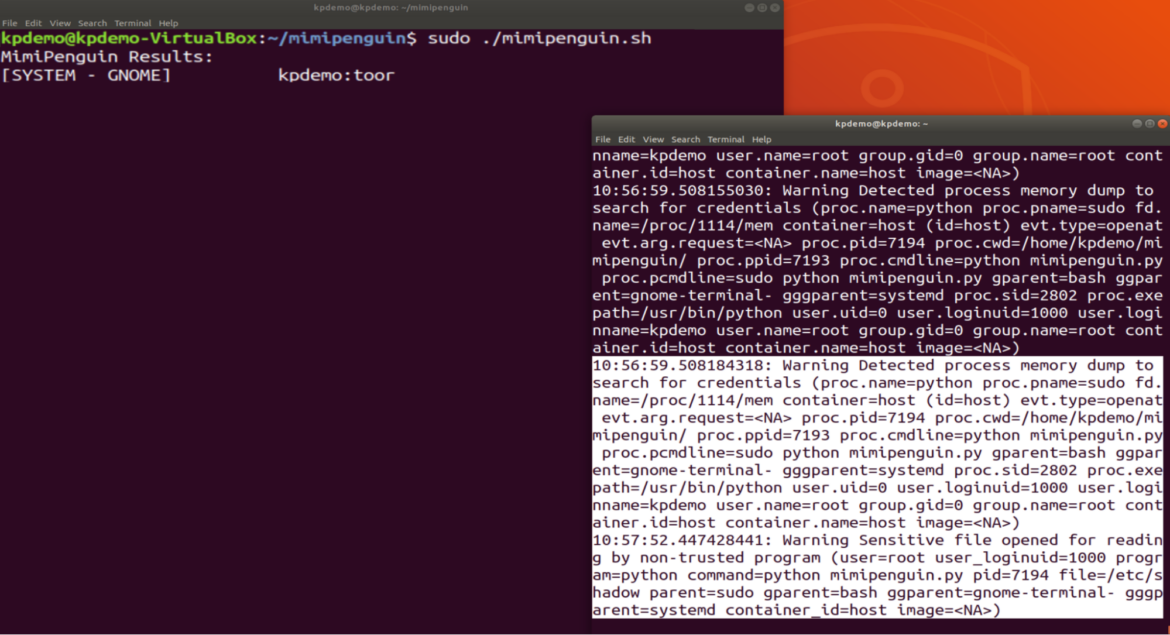
The tool tries to do something similar to the KeePass PoC but, in this case, it does not find the key (because the CVE is not implemented). However, it is able to obtain system credentials. In the image above, we can see both alerts; the first one is where it detects access to /proc/<pid>/mem.
10:56:59.508184318: Warning Detected process memory dump to search for credentials (proc.name=python proc.pname=sudo fd.name=/proc/1114/mem container=host (id=host) evt.type=openat evt.arg.request=<NA> proc.pid=7194 proc.cwd=/home/kpdemo/mimipenguin/ proc.ppid=7193 proc.cmdline=python mimipenguin.py proc.pcmdline=sudo python mimipenguin.py gparent=bash ggparent=gnome-terminal- gggparent=systemd proc.sid=2802 proc.exepath=/usr/bin/python user.uid=0 user.loginuid=1000 user.loginname=kpdemo user.name=root group.gid=0 group.name=root container.id=host container.name=host image=<NA>)<small><span class="shcb-language__paren"></span></small>
The second is where it gains access to /etc/shadow from where it extracts the user’s password.
10:57:52.447428441: Warning Sensitive file opened for reading by non-trusted program (user=root user_loginuid=1000 program=python command=python mimipenguin.py pid=7194 file=/etc/shadow parent=sudo gparent=bash ggparent=gnome-terminal- gggparent=systemd container_id=host image=<NA>)<small><span class="shcb-language__paren"></span></small>
LaZagne
The LaZagne project is an open source application used to retrieve lots of passwords stored on a local computer. In this case, it not only focuses on memory, but also searches for credentials using different techniques (plain text, API, custom algorithms, databases, etc.).
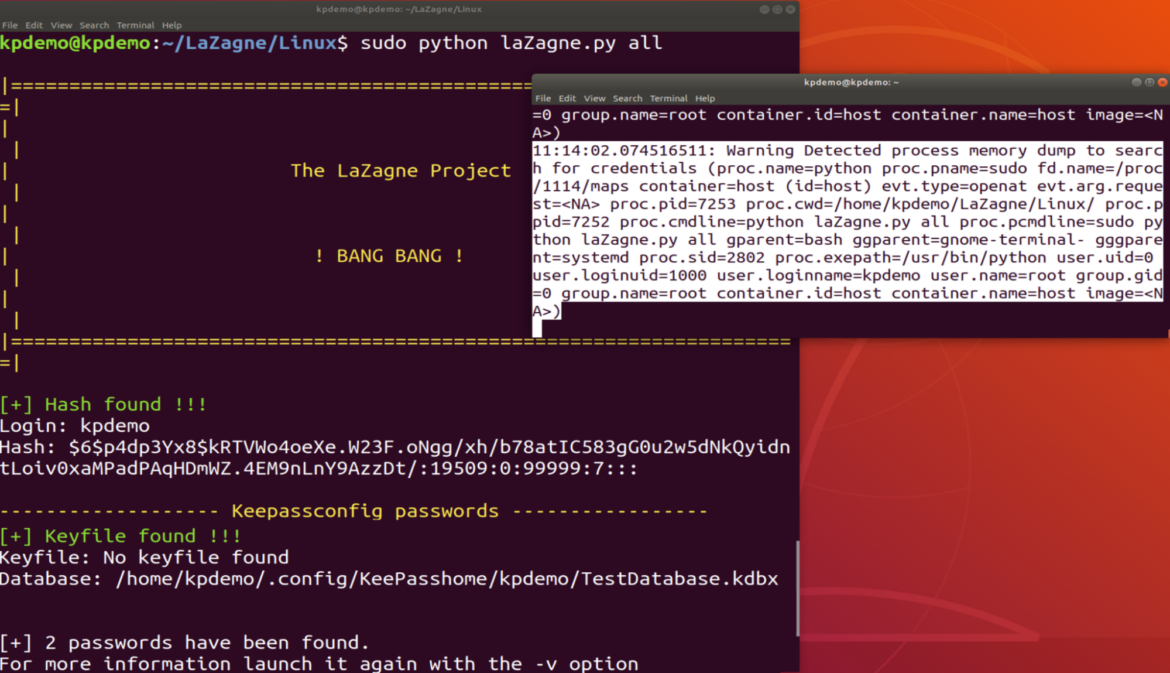
In this example, we have again the alert detecting the access again, and the tool shows us that it has found both the user’s password and the KeePass database that we had saved.
11:14:02.074516511: Warning Detected process memory dump to search for credentials (proc.name=python proc.pname=sudo fd.name=/proc/1114/maps container=host (id=host) evt.type=openat evt.arg.request=<NA> proc.pid=7253 proc.cwd=/home/kpdemo/LaZagne/Linux/ proc.ppid=7252 proc.cmdline=python laZagne.py all proc.pcmdline=sudo python laZagne.py all gparent=bash ggparent=gnome-terminal- gggparent=systemd proc.sid=2802 proc.exepath=/usr/bin/python user.uid=0 user.loginuid=1000 user.loginname=kpdemo user.name=root group.gid=0 group.name=root container.id=host container.name=host image=<NA>)<small> <span class="shcb-language__paren"></span></small>
Lesson learned
Harvesting credentials is a very common technique used by attackers. It is required to have all the necessary tools to detect these types of actions to prevent them from moving laterally or affecting other services.
Finally, we strongly recommend upgrading to the new version, KeePass 2.54.
Unlock Cloud Security Insights
Subscribe to our newsletter for the latest expert trends and updates
Related Articles:
Annual Threat Report 2026: What It Means for Security Leaders
Published: 06/08/2026
Top 6 Claude Security Risks to Watch as AI Becomes Your Employees' Operating System
Published: 06/02/2026
You Can't Patch a Running Plant: How Mythos Compresses the OT Security Timeline
Published: 06/02/2026









