Trust Model: The First Step to Ensure Your IT Network
Published 02/20/2024
Originally published by Devoteam.
What is Zero Trust?
Zero Trust is a security approach that mandates verification, employs least privilege, and operates under the assumption of a breach for every access request to a private network, irrespective of its origin or destination.
Its foundation rests on several principles to improve your security:
- Explicit Verification: All access attempts are authenticated and authorized based on a comprehensive set of data points, including user identity, location, device health, service or workload, data classification, and anomalies.
- Least Privilege Access: Access is restricted to the bare minimum necessary using techniques such as just-in-time and just-enough access (JIT/JEA), risk-based adaptive policies, and data protection measures, thus securing both data and productivity.
- Assume Breach: To minimize the impact of potential breaches, access is segmented, and the blast radius is reduced. End-to-end encryption is validated, and analytics are utilized for visibility, threat detection, and defense enhancement.
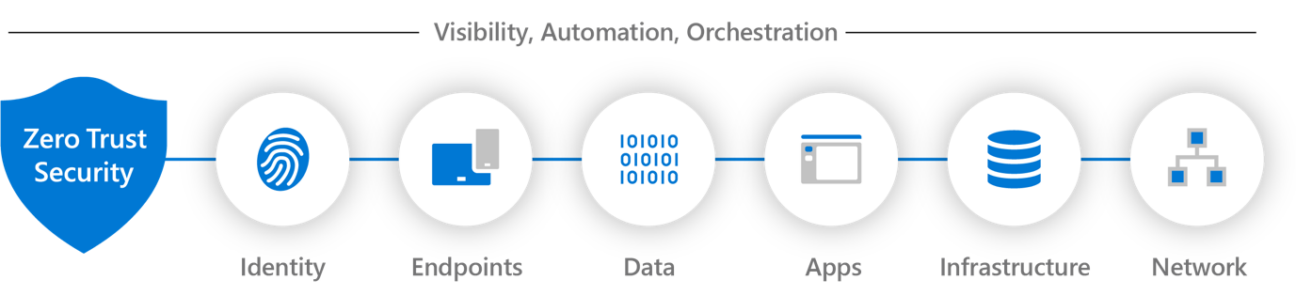
Zero Trust extends across six core elements:
- Identities: People, services, and IoT components are verified and authorized based on multiple data points, such as user identity, location, and device health.
- Devices: Endpoints accessing the network are monitored for compliance with device health standards and updated regularly.
- Apps and APIs: Applications and services running on the network are secured with appropriate permissions, configurations, and vulnerability scans.
- Data: Information flowing through the network is protected using encryption, classification, and access policies, while anomalies are monitored.
- Infrastructure: Physical and virtual resources hosting the network are hardened against attacks and segmented to minimize breach impact.
- Networks: Connections between elements are controlled using segmentation, encryption, and analysis, and verified end-to-end.
This approach require a comprehensive and integrated security strategy encompassing the entire digital infrastructure.
Some benefits of Zero Trust security include:
- Enhanced Employee Experience: Employees can securely work from any location and on any device.
- Facilitated Digital Transformation: Intelligent security supports complex and hybrid environments.
- Reduced Vulnerabilities: Granular policies and closed security gaps minimize security risks and lateral movement.
- Protection from Threats: Layered defense explicitly verifies all access requests, safeguarding against internal and external threats.
- Regulatory Compliance: Helps comply with evolving regulatory requirements by offering a consistent and transparent data protection strategy.
How does it work in Office 365?
Zero-trust works in Office 365 by applying the following security capabilities:
- Conditional Access: This allows you to enforce granular policies based on user, device, app, location, and risk factors. For example, you can require multifactor authentication, device compliance, or app protection for accessing specific resources or data.
- App protection policies: This allows you to protect the data within Office 365 apps on mobile devices, such as Outlook, Word, Excel, etc. For example, you can restrict copy-paste, screen capture, or external sharing of sensitive data.
- Device compliance policies: This allows you to check the health and compliance status of devices that access Office 365. For example, you can require devices to have a PIN, encryption, antivirus, or latest updates.
- Microsoft Defender for Office 365: This provides threat protection and intelligence for Office 365 apps and services, such as email, SharePoint, Teams, etc. For example, it can detect and block phishing, malware, ransomware, or spoofing attacks.
How to apply Zero Trust principles to Azure infrastructure as a service (IaaS)?
Zero Trust in the context of Infrastructure as a Service (IaaS) in Azure refers to a security model where no implicit trust is granted to assets based on their location (inside or outside the network) or on their identity (whether they are external or internal users).
In a traditional security model, once someone gains access to the network, they might be trusted to access various resources within that network.
Zero Trust, on the other hand, assumes that threats could come from both inside and outside the network, and thus, trust should not be granted based solely on the user’s location or identity.
In Azure IaaS, Zero Trust is implemented through various security measures and technologies:
- Identity and Access Management (IAM): Azure Active Directory (AAD) is often used to manage user identities and their access to Azure resources. With Zero Trust, access controls are enforced based on a user’s identity, their role, and other contextual factors such as the device being used and the location from which the access is attempted.
- Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring users to provide multiple forms of authentication before granting access. This could include something they know (like a password) and something they have (like a mobile device for receiving a verification code).
- Conditional Access Policies: Azure allows administrators to define policies that control access to resources based on certain conditions, such as the user’s location, device health, or the sensitivity of the resource being accessed. This ensures that access is granted only when specific conditions are met.
- Network Segmentation: Azure Virtual Networks (VNETs) can be segmented into smaller, isolated networks using Network Security Groups (NSGs) and Virtual Network Service Endpoints (VNET service endpoints). This helps in minimizing the attack surface and containing potential breaches within specific segments of the network.
- Encryption: Azure offers various encryption options to protect data both at rest and in transit. This includes Azure Disk Encryption for encrypting virtual machine disks, Azure Storage Service Encryption for encrypting data stored in Azure Storage, and Azure VPN Gateway for encrypted communication between virtual networks.
- Continuous Monitoring and Threat Detection: Azure Security Center provides continuous monitoring of Azure resources and detects potential security threats using advanced analytics and machine learning algorithms. It can identify suspicious activities and recommend actions to mitigate risks.
- Just-In-Time (JIT) Access: Azure Security Center allows administrators to restrict access to Azure VMs by enabling JIT access. This means that access to VMs is only granted when needed and for a limited time window, reducing the attack surface and minimizing the risk of unauthorized access.
What are the key success factors to set-up a Zero Trust Model in your company?
Instead of assuming everything behind the corporate firewall is safe, the Zero Trust model assumes breach and verifies each request as though it originates from an open network.
Regardless of where the request originates or what resource it accesses, Zero Trust teaches us to “never trust, always verify.” Every access request is fully authenticated, authorized, and encrypted before granting access. Microsegmentation and least-privilege access principles are applied to minimize lateral movement. Rich intelligence and analytics are utilized to detect and respond to anomalies in real time.
For example:
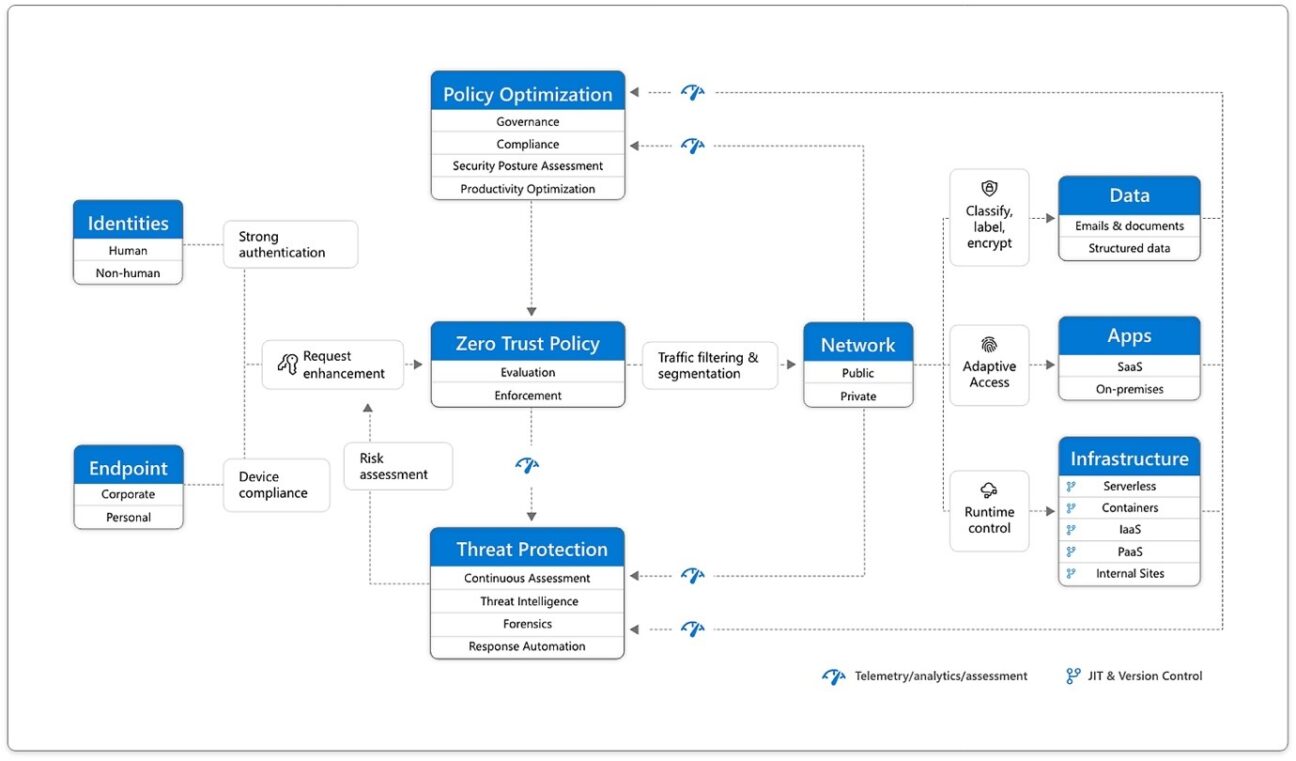
Zero Trust should cover your whole digital environment—including identities, endpoints, network, data, apps, and infrastructure. Zero Trust architecture is a complete end-to-end plan that needs integration across the elements. The basis of Zero Trust security is identities. Both human and non-human identities need strong authorization, connecting from either personal or corporate endpoints with compliant devices, asking for access based on strong policies based on Zero Trust principles of explicit verification, least-privilege access, and assumed breach. As a unified policy enforcement, the Zero Trust policy stops the request, explicitly verifies signals from all six basic elements based on policy configuration and allows least-privilege access. Signals include the user’s role, location, device compliance, data sensitivity, and app sensitivity. Besides telemetry and state information, the risk assessment from threat protection inputs into the policy engine to automatically deal with threats in real time. Policy is applied at the time of access and continuously checked throughout the session. This policy is further improved by policy optimization. Governance and compliance are essential to a strong Zero Trust implementation. Security posture assessment and productivity optimization are needed to measure the telemetry across the services and systems. The telemetry and analytics inputs into the threat protection system. Large amounts of telemetry and analytics enriched by threat intelligence produces high-quality risk assessments that can be either manually investigated or automated. Attacks occur at cloud speed and, because humans can’t react fast enough or go through all the risks, your defense systems must also act at cloud speed. The risk assessment inputs into the policy engine for real-time automated threat protection and additional manual investigation if needed. Traffic filtering and segmentation is applied to the evaluation and enforcement from the Zero Trust policy before access is given to any public or private network. Data classification, labeling, and encryption should be applied to emails, documents, and structured data. Access to apps should be adaptive, whether SaaS or on-premises. Runtime control is applied to infrastructure with serverless, containers, IaaS, PaaS, and internal sites with just-in-time (JIT and version controls actively engaged. Finally, telemetry, analytics, and assessment from the network, data, apps, and infrastructure are fed back into the policy optimization and threat protection systems.
Unlock Cloud Security Insights
Subscribe to our newsletter for the latest expert trends and updates
Related Articles:
What Recent Medical Device Breaches Reveal About Security Gaps in the Cloud
Published: 05/21/2026
Toxic Combinations: The Five Powers Fueling the Agentic Threat Landscape
Published: 05/20/2026
Combatting the Top Three Sources of Risk in the Cloud
Published: 05/18/2026






.jpeg)
.jpeg)
.jpeg)
